Developer Support
Advocacy and Innovation
Latest posts

Comment l’IA générative impacte-t-elle l’expérience développeur?
Adlene Sifi explore l'impact de l'IA générative sur l'expérience des développeurs. Dans cet article, nous allons tenter de déterminer s’il existe un lien entre l’utilisation de l’IA générative (ex. : GitHub Copilot) et l’expérience développeur (DevEx). Nous souhaitons vérifier plus précisément si l’utilisation de l’IA générative a un impact positif sur l’expérience développeur. Nous tenterons même de vérifier s’il existe un lien de causalité entre l’utilisation de l’IA générative et l’amélioration de l’expérience développeur. Nous allons dans un premier temps commencer par définir ces deux concepts. ...

How does generative AI impact Developer Experience?
Adlene Sifi explores the impact of generative AI on developer experience. In this article, we will try to determine if there is a link between the use of generative AI (e.g., GitHub Copilot) and developer experience (DevEx). Specifically, we aim to verify whether the use of generative AI has a positive impact on developer experience. We will even try to see if there is a causal link between the use of generative AI and the improvement of developer experience. First, let's define these two concepts. What is developer experience? Is it a new buzzword? A market trend? Worse, is it a new marketing tactic...

Supercharge Developer Workflows with GitHub Copilot Workspace Extensions
David Minkovski takes you on a hands-on journey to extend GitHub Copilot beyond just being a code assistant — turning it into a true AI-powered teammate inside VS Code. Motivation It is 2025 and Software Developers are faced with an incredibly fast-paced high-tech landscape — full of innovation and automation around every corner. Even with the consideration of AI taking on many roles (and hopefully not our jobs just yet) we are constantly challenged with rising complexities of distributed systems, cloud-native architectures and cognitive loads as well as context switching and endless interruptions. I c...

AI-Powered Customer Support: The Ultimate Multi-Agent System
David Minkovski explores using Azure OpenAI and Rust to Build Intelligent and Scalable AI Systems Motivation For the past few months, I’ve had the pleasure of taking the front seat to some really fascinating and exciting AI projects, thanks to my amazing customers and colleagues at Microsoft. During these sessions, I noticed a common challenge: How do I use ChatGPT while keeping control? So, I thought to myself, why not write a little article to help? Let’s break it down and create a super simple “multi-agent” system. This system will handle everything from the initial customer support request to e...

Deploying WebJobs to Azure Container Apps
Debjyoti Ganguly walks through the process of migrating existing WebJobs to Azure Container App Jobs, highlighting the benefits and providing practical steps to implement this migration effectively Introduction As businesses scale, the need for a robust and scalable environment for running background jobs becomes essential. Azure Container App Jobs offer a modern, scalable, and containerized solution for running background jobs, providing significant benefits over traditional Azure WebJobs. This guide will walk you through the process of migrating existing WebJobs to Azure Container App Jobs, highlighting...
AI: The New Frontier for Developers
AJ Enns reflects on his journey as a new developer and the impact of AI as an integrated, coding assistant for improving developer velocity. The year is 2024, and AI has been around for a while. ChatGPT broke onto the scene and changed the world forever. As soon as I heard about it, the first thing I did was try to learn Blazor with the help of AI. Within 3 weeks, I had a working example in a language I did not know before, as a result I was hooked. How do I share my recent learnings and amazement? Working as a Developer Advocate, I quickly learned that both the Developer and the Business were not early ad...

Debugging a managed identity connection to Azure SQL in Azure App Service using containers
Dominique St-Amand explores how to debug a managed identity connection from a container-based App Service to Azure SQL. So you’ve been eager to deploy your containerized web application that you’ve been working on for a while, to Azure App Service. You follow the best security practices which means you’ve setup your connection to your Azure SQL database using a managed identity. Upon loading your application, you get a dreadful exception that you can’t connect to the database. You then wonder, is this a database permission problem or some another problem, such as the application cannot connect to the datab...

Autogen RAG
Linkai Yu explores the retrieval-augemented generation pattern with Azure OpenAI Assistants API. The Retrieval-Augmented Generation (RAG) pattern is the standard for integrating ground AI with local data. One powerful way to implement RAG is through the function call or tool call feature in the Function Call API. When examining the samples provided by the Azure OpenAI Assistant API Function Call, Completion API Function Call, or Autogen Function Call, they all require the function metadata to be specified in the code. Imagine you have hundreds of data I/O functions, ranging from SQL queries to microservice...
Boosting Azure DevOps Security with GHAS Code Scanning
Debjyoti Ganguly shares insights on the security benefits and configuration of GHAS Code Scanning with Azure DevOps. Boosting Azure DevOps Security with GHAS Code Scanning Code scanning, a pipeline-based tool available in GitHub Advanced Security, is designed to detect code vulnerabilities and bugs within the source code of ADO (Azure DevOps) repositories. Utilizing CodeQL as a static analysis tool, it performs query analysis and variant analysis. When vulnerabilities are found, it generates security alerts. CodeQL CodeQL is a powerful static analysis tool used for showing vulnerabilities and bugs in so...

Running Open AI Whisper on Azure
Monu Bambroo explores Whisper, a speech to text model from OpenAI that you can use to transcribe audio files. The model is trained on a large dataset of English audio and text. The model is optimized for transcribing audio files that contain speech in English. The model can also be used to transcribe audio files that contain speech in other languages. Whisper is an advanced automatic speech recognition (ASR) system, developed using 680,000 hours of supervised multilingual and multitask data from the web. This extensive and diverse data set enhances its ability to handle various accents, background noise, a...
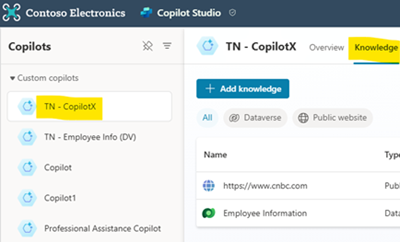
Copilot Studio – Prompt Response Times
Tahir Naveed walks through how to measure prompt response times with Microsoft Copilot Studio and explores considerations that factor into the overall performance of these requests. Building custom copilots (GenAI chatbots) in Microsoft Copilot Studio is amazing. Especially with the new functionalities which were released in Microsoft Build 2024. What’s more amazing is when we can point the custom copilots to different kinds of external and internal data sources like public websites (external), Dataverse tables (internal), SharePoint etc. Today we will be looking at how to check the response time of a p...
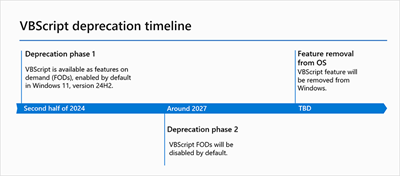
VBScript deprecation: Timelines and next steps
Scripting options for web development and task automation are modernizing. To provide you with the most modern and efficient options, we are replacing VBScript with more advanced alternatives such as JavaScript and PowerShell. Find out what VBScript deprecation means for you and how you can get ready. What is VBScript? Visual Basic Scripting Edition, commonly referred to as VBScript, is a lightweight scripting language first introduced by Microsoft in 1996. The language has been available as a system component in Windows OS and has been widely used for automating tasks and controlling applications on Windows-ba...
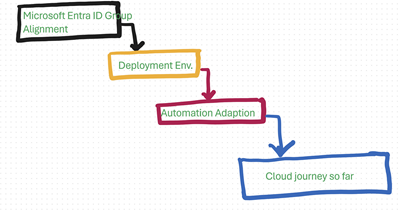
Azure CI/CD: Govern seamlessly from start to finish
Debjyoti Ganguly shares insights on a resilient end-to-end cloud governance framework for Azure CI/CD pipelines. Hey there, tech enthusiasts! This article serves as a technical guide to implementing a resilient end-to-end cloud governance framework for Azure CI/CD pipelines. It is designed to be vendor-agnostic and aligns seamlessly with enterprise security objectives, considerations, and compliance requirements. Throughout this discourse, we will employ the Azure Role-Based Access Control (RBAC) model, a familiar concept utilized within the Azure Resource Manager framework. Decisive Process Deconstructi...
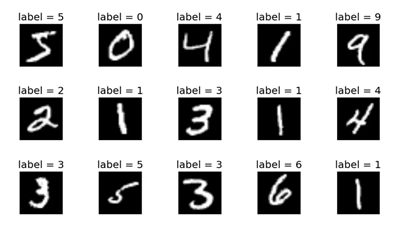
Azure Machine Learning Service for Kubernetes Architects: Deploy Your First Model on AKS with AZ CLI v2
Joseph Masengesho provides a step-by-step tutorial on how to deploy your first ML model on AKS. In a previous post, I provided a lengthy write-up about my understanding of using Kubernetes as a compute target in Azure ML from a Kubernetes architect’s perspective. In this post, I will offer a step-by-step tutorial that teaches you how to deploy your first ML model on AKS. As a disclaimer, I am not a data scientist; however, I work with customers who deploy ML workloads on Kubernetes. In this tutorial, we will deploy a trained regression model based on the MNIST Dataset, which consists of 60K handwritten digi...
How to visualize Semantic Kernel & Azure OpenAI plans using Mermaid
Jordan Bean explores how to visualize Semantic Kernel & Azure OpenAI plans using Mermaid. Using the function calling ability of Semantic Kernel/OpenAI is very exciting from an application development point of view. Instead of hard-coding paths though the system, Semantic Kernel & OpenAI can decide for themselves what plugins to call, the order of operations, parsing input & output, etc. However, it can be challenging to understand why the system decided to go down a path & all of the operations, prompts, function calls, etc. that occurred. Semantic Kernel provides a class that record...

Azure DevOps Pipelines: Discovering the Ideal Service Connection Strategy
John Folberth explores various configurations, decisions, and pros/cons that should be evaluated when deciding how your DevOps environment will deploy code into Azure. About This post is part of an overall series on Azure DevOps YAML Pipelines. The series will cover any and all topics that fall into the scope of Azure DevOps Pipelines. I encourage you to check it out if you are new to this space. Introduction When an organization is trying to configure their Azure DevOps (ADO) environment to deploy into Azure, they are immediately met with the dilemma on how their DevOps instance will execute the deploy...
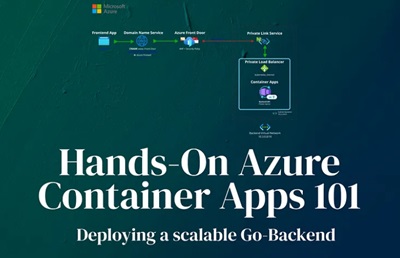
Hands-On Azure Container Apps 101 — Deploying a scalable Go-Backend
David Minkovski shares a hands-on guide to explore the power and simplicity of Azure Container Apps and Azure Front Door as a great alternative to Azure Kubernetes Services and other Kubernetes implementations for developers. Motivation I am sure you have seen the world go crazy about Kubernetes and while this technology is amazing and has many benefits, the complexities of managing these clusters can be quite, how shall I put this…challenging. Well lucky for us Microsoft has come up with some real magic — Embrace the simplicity and power of Azure Container Apps and enjoy hassle-free web app deployment....
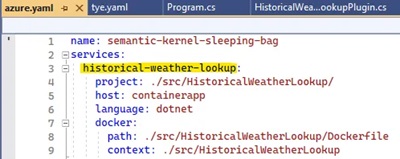
How to enhance your chatbot so it can retrieve data from multiple data sources & orchestrate its own plan with C# Semantic Kernel, planner & Azure OpenAI – part 4 (local development & deployment details)
In this multi-part series, Jordan Bean shares how to enhance a chatbot to retrieve data from multiple data sources and orchestrate plans with C# Semantic Kernel, planner, and Azure Open AI. In the previous post, I detailed how the demo app runs. In this post, let’s talk about some of the techniques & technologies I used to make the demo easy to deploy & run. Here is the link to the GitHub repo. Project Tye Project Tye is an open-source project that makes it easy to stand up a microservice-based application locally. It is easy to run any individual API or web app, such as running or . Ho...
