In today’s Microsoft Graph Mailbag post, we cover Azure AD applications and users for testing Microsoft Graph queries in a development environment.
Please be sure to follow this blog series using https://aka.ms/MSGraphMailbag or with RSS using https://developer.microsoft.com/graph/blogs/feed/?tag=MSGraphMailbag.
Introduction
When developing solutions powered by Microsoft Graph, I like to think through the different authentication flows that are involved. I ask myself questions such as the following:
- Will users interactively log in to the application?
- Does the user need to have an elevated Azure AD role assignment?
- Does the user have any conditional access policies that may be applied?
- What type of credential (password, client secret, client certificate, etc.) will be used?
As members of the Microsoft Graph Customer and Partner Experience (CPx) team, our team tests Microsoft Graph requests almost every day. This includes validating new APIs, prototyping solutions, investigating scenarios with customers and partners, and more. Generally, we are testing across a wide variety of hosting environments – Microsoft Graph PowerShell SDK, Postman, and numerous web apps to name a few. As such, it is helpful to have the required components for authentication already configured in a Microsoft 365 developer tenant so we can quickly and easily test the necessary Microsoft Graph endpoints.
Note: If you don’t have a developer tenant, you can sign up for one through our Microsoft 365 Developer Program.
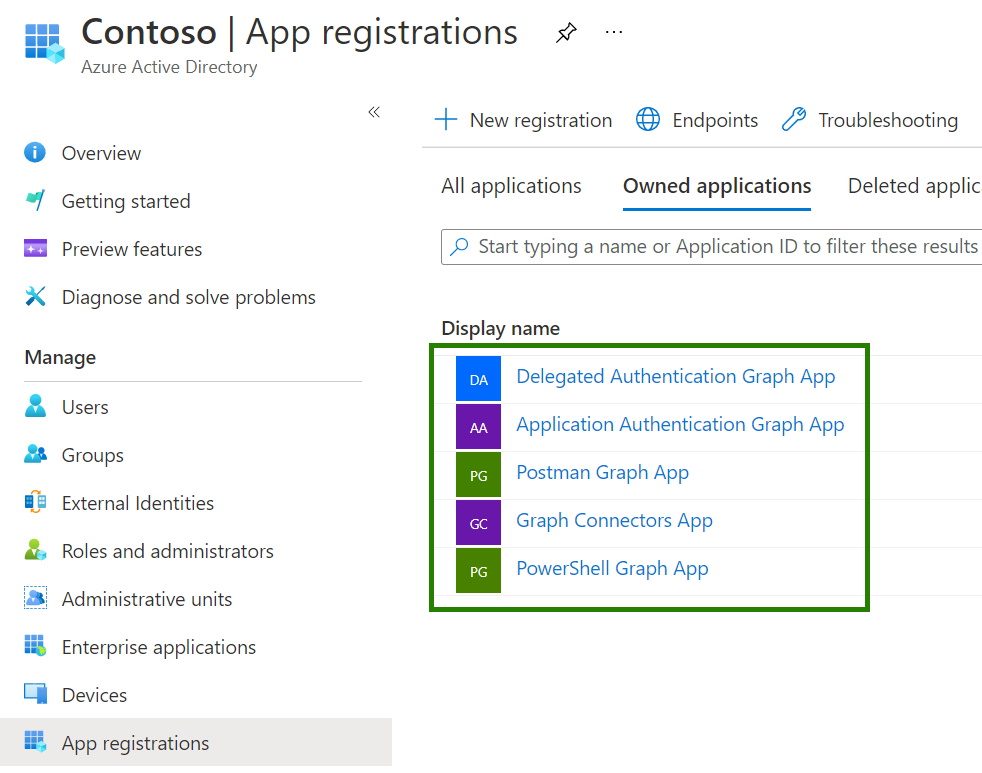
Sample Azure AD applications
I provision a few sample Azure AD applications in my development environment. The primary applications include:
- Delegated Authentication Graph App
- Intended for delegated authentication flows such as device code or authorization code flow
- Allow public client flow
- Enable implicit grant for access tokens and ID tokens
- Application Authentication Graph App
- Intended for application authentication flows such as client credentials flow
- Configured with client secret and certificate for authentication
- Postman Graph App
- Intended for delegated or application authentication flows
- Redirect URI(s) for Postman callback
- Graph Connectors App
- Intended for application authentication flow
- ExternalItem.ReadWrite.All permission for ingesting content
- PowerShell Graph App
- Intended for delegated or application authentication flows
- Configured with client secret and certificate for authentication
- Separate application since generally testing administrative requests with different permissions
Sample Azure AD users
Aside from testing with different Azure AD applications, I also find it helpful to have a variety of Azure AD users with different configurations. When using a delegated authentication flow, there are a few Microsoft Graph endpoints that require an Azure AD role assignment or Azure AD licensing in addition to normal delegated permissions. The following list is not exhaustive and only a point in time reference as of publish date.
- Azure AD domain administrator
- Reports Reader
- Security Administrator / Security Reader
- Azure AD P1/P2 licensed user
Automate creating Azure AD resources
Having sample Azure AD application and users in a single development environment is helpful, but it is better if I can make this a repeatable process. In a future post I will cover the details of automating the creation of these resources. For today’s post though I’m sharing a few automation options to explore.
- Microsoft Graph PowerShell SDK
- PowerShell SDK installation
- Example commands
- New-MgApplication
- New-MgUser
- Microsoft365DSC
- Microsoft Graph CLI (preview)
Conclusion
Having the right Azure AD components ready for testing Microsoft Graph requests can help speed up development when iterating on a solution. In this post, I covered a few questions about the authentication flows or users involved as well as sample Azure AD applications and users to pre-configure in a Microsoft 365 developer tenant.
Today’s post was written by Brian T. Jackett, Senior Program Manager on the Microsoft Graph CPx team. Join us for our next post June 8, 2021.

0 comments