Summary: Thomas Rayner, Microsoft Cloud & Datacenter Management MVP, shows how to delete your Windows CA certificates and crypto provider as a part of migrating a Windows certification authority from CSP to KSP and from SHA-1 to SHA-256.
Hello! I’m Thomas Rayner, a proud Cloud & Datacenter Management Microsoft MVP, filling in for The Scripting Guy this week. You can find me on Twitter (@MrThomasRayner) or on my blog, Working Sysadmin: Figuring stuff out at work.
I recently had the chance to work with Microsoft PFE, Mike MacGillivray, on an upgrade of some Windows certification authorities, and I want to share some information about it with you. This script has only been tested on Windows Server 2012 and later.
Note This is a five-part series that includes the following posts:
- Migrate Windows CA from CSP to KSP and from SHA-1 to SHA-256: Part 1 Explore why you may need to perform this work, configure logging, and set up variables.
- Migrate Windows CA from CSP to KSP and from SHA-1 to SHA-256: Part 2 Back up your certification authority (CA) and test the script.
- Migrate Windows CA from CSP to KSP and from SHA-1 to SHA-256: Part 3 Delete the certificate and crypto provider so they can be rebuilt as a KSP and SHA-256 solution.
- Migrate Windows CA from CSP to KSP and from SHA-1 to SHA-256: Part 4 Import keys and certificate into a KSP.
- Migrate Windows CA from CSP to KSP and from SHA-1 to SHA-256: Part 5 Modify the registry for SHA-256.
Now let’s delete a bunch of things!
There’s a lot of stuff to delete so we can re-create it properly. Before we do anything else, let’s stop the certificate service:
Stop-Service -Name ‘certsvc’
Add-LogEntry $Logpath ‘CA service stopped’
Now let’s retrieve and record the serial number of our certificate:
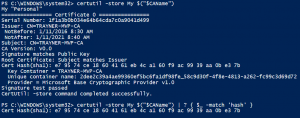
$CertSerial = cmd.exe /c “certutil -store My $(“$CAName”)” | Where-Object -FilterScript {
$_ -match ‘hash’
}
$CertSerial | Out-File -FilePath “$Drivename\$Foldername\CA_Certificates.txt”
Add-LogEntry $Logpath ‘Got CA cert serials’
This certutil command gets the certificates in the store of my CA. I’m using Where-Object to find the hash (or serial number) of my certificates. You can see the difference in this screenshot:
Then, I write the output to CA_Certificates.txt in my working folder, in case I need it again.
Next up, certificate providers! It’s almost the same command. I’m going to save the providers in CSP.txt:
$CertProvider = cmd.exe /c “certutil -store My $(“$CAName”)” | Where-Object -FilterScript {
$_ -match ‘provider’
}
$CertProvider | Out-File -FilePath “$Drivename\$Foldername\CSP.txt”
Add-LogEntry $Logpath ‘Got CA CSPs’
Now it’s time to cowboy up and delete some stuff! First, let’s delete the certificate:
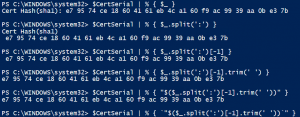
$CertSerial | ForEach-Object -Process {
cmd.exe /c “certutil -delstore My `”$($_.Split(‘:’)[-1].trim(‘ ‘))`””
}
Add-LogEntry $Logpath ‘Deleted CA certificates’
That looks pretty interesting. Let me break down the weird bit of string manipulation I’m doing:
- The first line writes the value of $CertSerial.
- The next splits it on the colon character.
- The third line selects only the line with the serial number.
- Then I’m trimming the whitespace off each end.
- Now on line 5, I’m trying to put quotation marks around the serial number, but PowerShell thinks I’m trying to denote that this is a string. The problem is that the certutil command needs the quotation marks to be passed. Otherwise, it thinks each little part of the serial number is a different argument.
- So on line 6, I’m escaping the quotation marks with the backtick character. This lets the –delstore argument of certutil accurately delete your certificate.
Next is deleting the provider. It’s going to be pretty similar to how I just deleted the certificate.
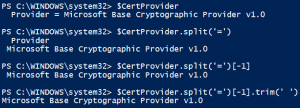
$CertProvider | ForEach-Object -Process {
cmd.exe /c “certutil -CSP `”$($_.Split(‘=’)[-1].trim(‘ ‘))`” -delkey $(“$CAName”)”
}
Add-LogEntry $Logpath ‘Deleted CA private keys’
I’ll break this one down, too. The differences are that I’m not in a foreach loop, and I’m splitting on the equals ( = ) character. I still have to wrap this in escaped quotation marks, too (not pictured).
Let’s pop this in a Try/Catch block and add a little more logging, shall we?
Clean slate! Tomorrow I’m going to show you how to import the keys into a KSP and get that all into your CA’s certificate store. Upgrading from CSP to KSP and SHA-1 to SHA-256 is a pretty involved process but we’re more than half way done.
If you are in a big hurry and want the full script, you can find it on my blog: Upgrade Windows Certification Authority from CSP to KSP and from SHA-1 to SHA-256. I’d sincerely recommend reading all of the posts in this series first, though, so you understand what it is you’re running.
~Thomas
I invite you to follow me on Twitter and Facebook. If you have any questions, send email to me at scripter@microsoft.com, or post your questions on the Official Scripting Guys Forum. Also check out my Microsoft Operations Management Suite Blog. See you tomorrow. Until then, peace.
Ed Wilson, Microsoft Scripting Guy


0 comments