App Dev Manager Vijetha Marinagammanavar spotlights secure access to Azure VMs using Bastion.
In this blog post, I am going to introduce you to Azure Bastion and show how to create your first Azure Bastion host.
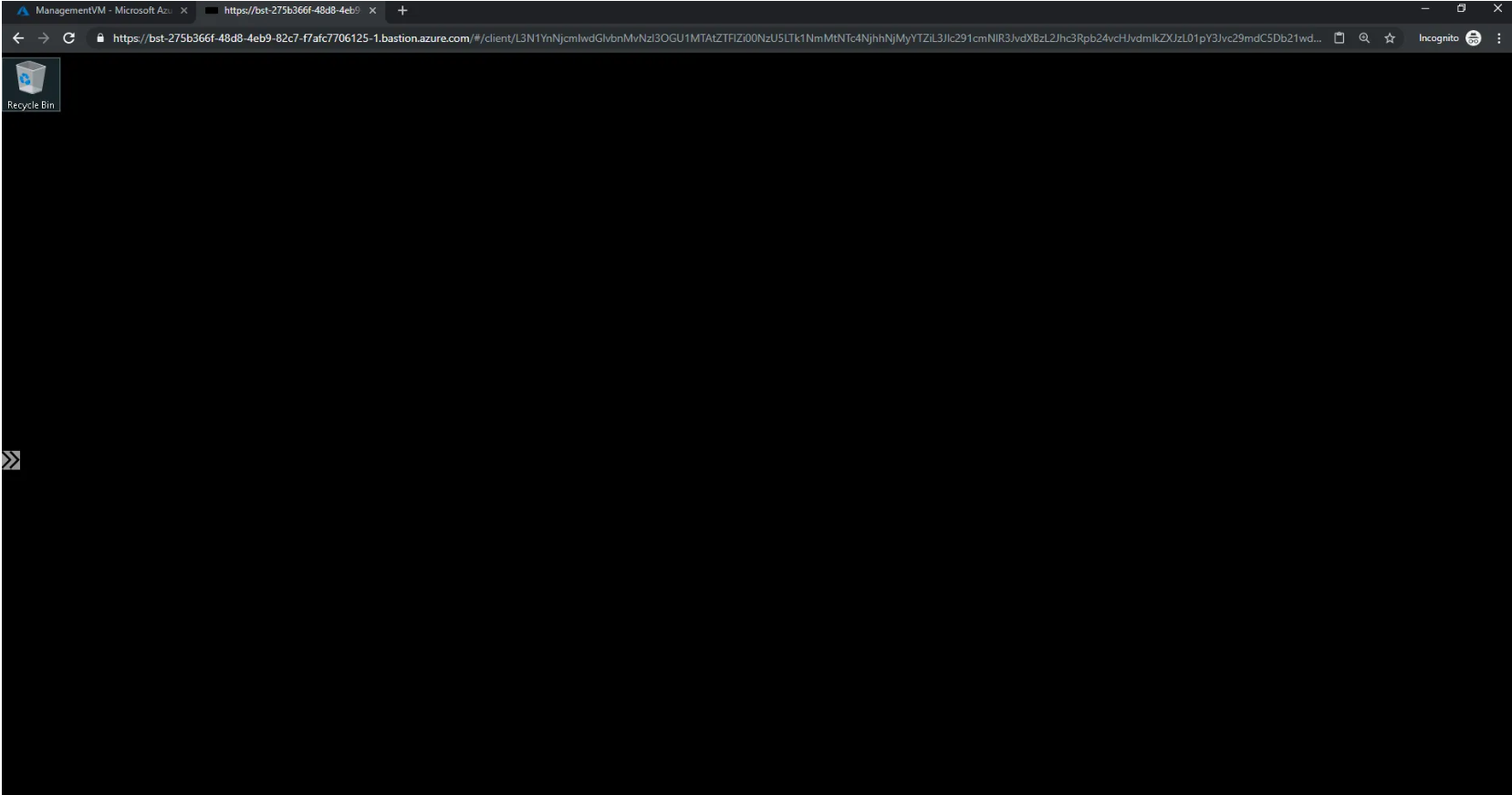
Azure Bastion is a new fully platform-managed PaaS service. It provides secure and seamless RDP/SSH connectivity to your virtual machines directly in the Azure portal over SSL. When you connect via Azure Bastion, your virtual machines do not need a public IP address.
Customers connecting to VM’s on private networks face security risks all the time. Exposing network assets to the public internet through Remote Desktop Protocol and Secure Shell increases the security perimeter, making it harder to manage and protect them. Azure Bastion is provisioned directly in a customer’s Virtual Network and supports all VMs in their VNet using SSL, without any exposure through public IP addresses.
Azure Bastion service is generally available now. This blog will provide a quick introduction of the service and steps to enroll the service in the environment to reach Azure VMs (Windows) over a secure way.
The availability of Azure Bastion is updated on Microsoft documentation. Please refer to https://docs.microsoft.com/en-us/azure/bastion/bastion-overview for region availability and pricing.
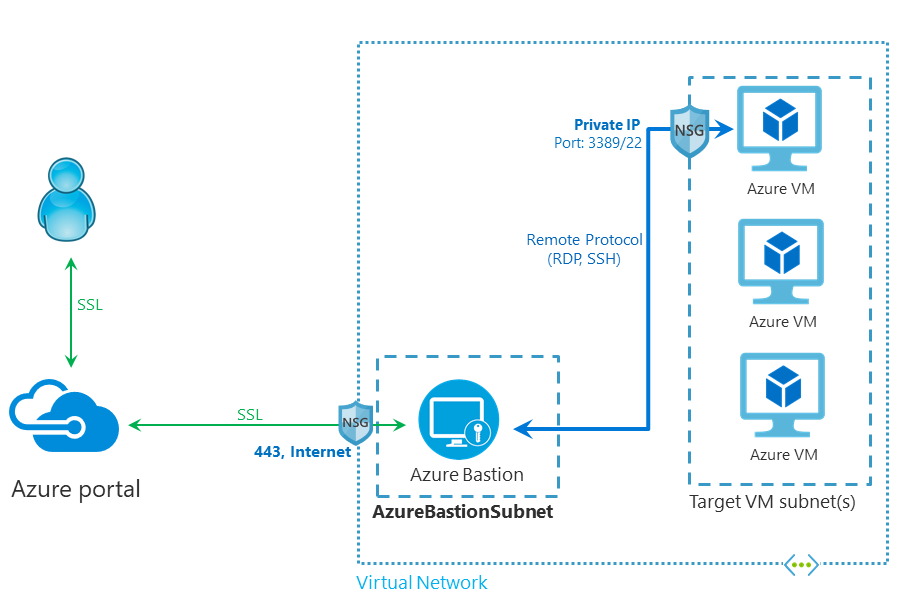 Azure Bastion architecture
Azure Bastion architecture
Key features
- RDP and SSH directly in the portal
- Remote session over SSL for SSH/RDP
- No public IP needed on the Azure VM
- No need for an Agent inside the Azure VM
- Browser support for Edge and Google Chrome
Create an Azure Bastion Resource
- There are two ways to deploy an Azure Bastion Host over the Portal or via the Azure VM Blade.
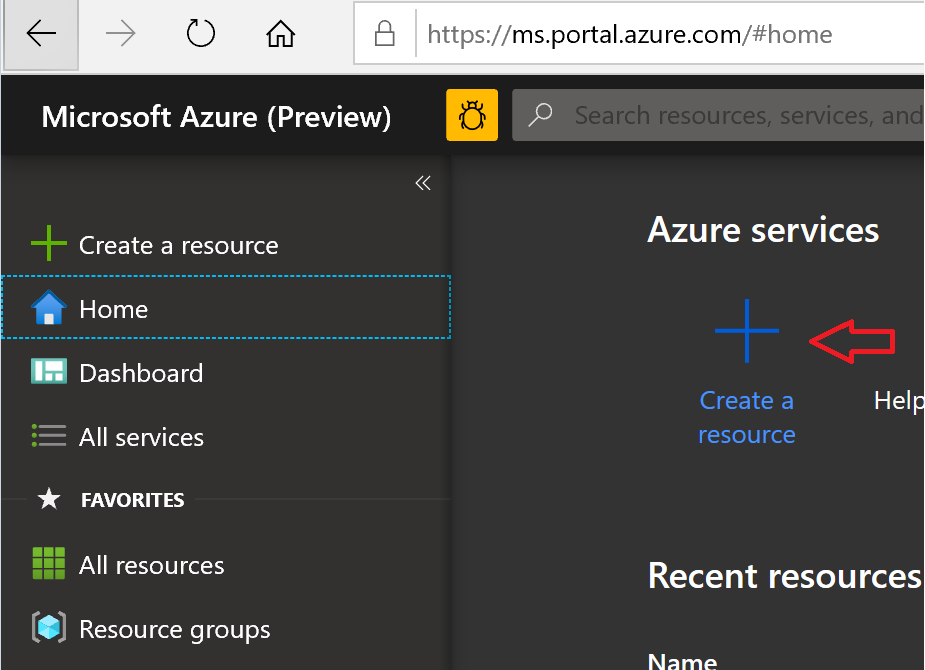
- Login to your Azure portal and click “Create a new resource”.
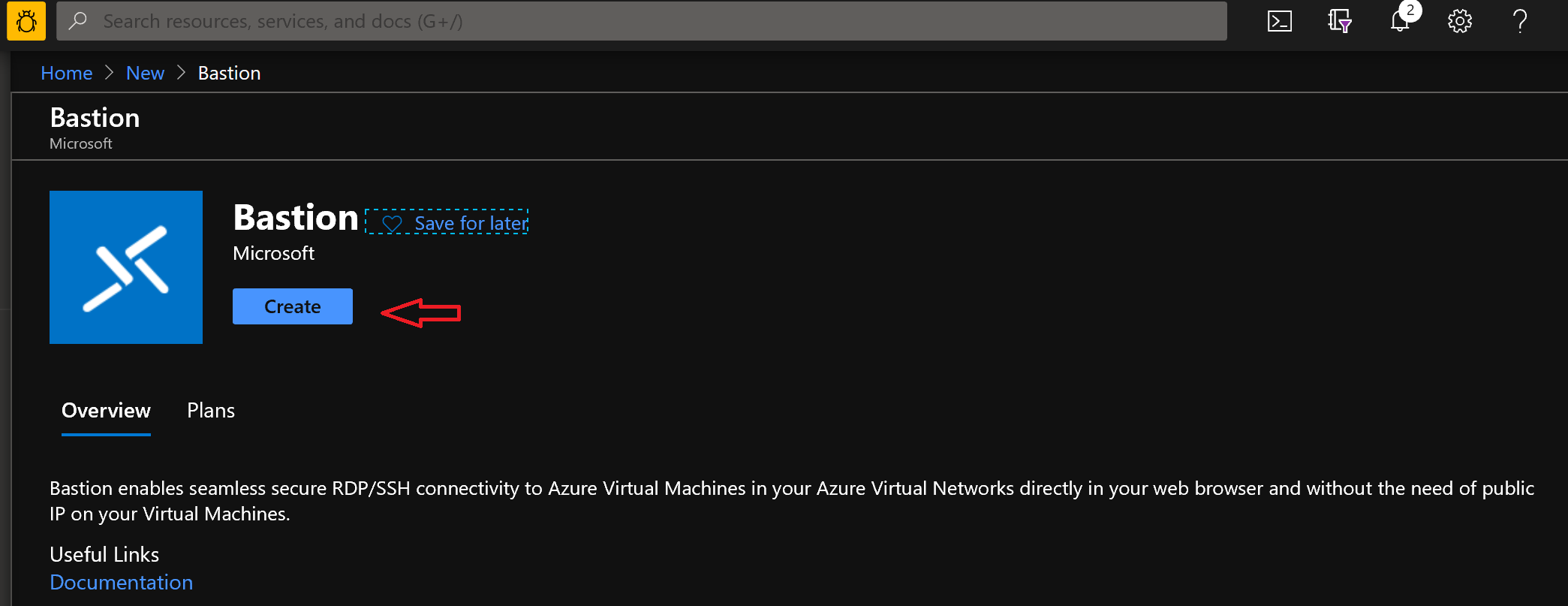
- Then search for Bastion. Click Create to start the deployment wizard.
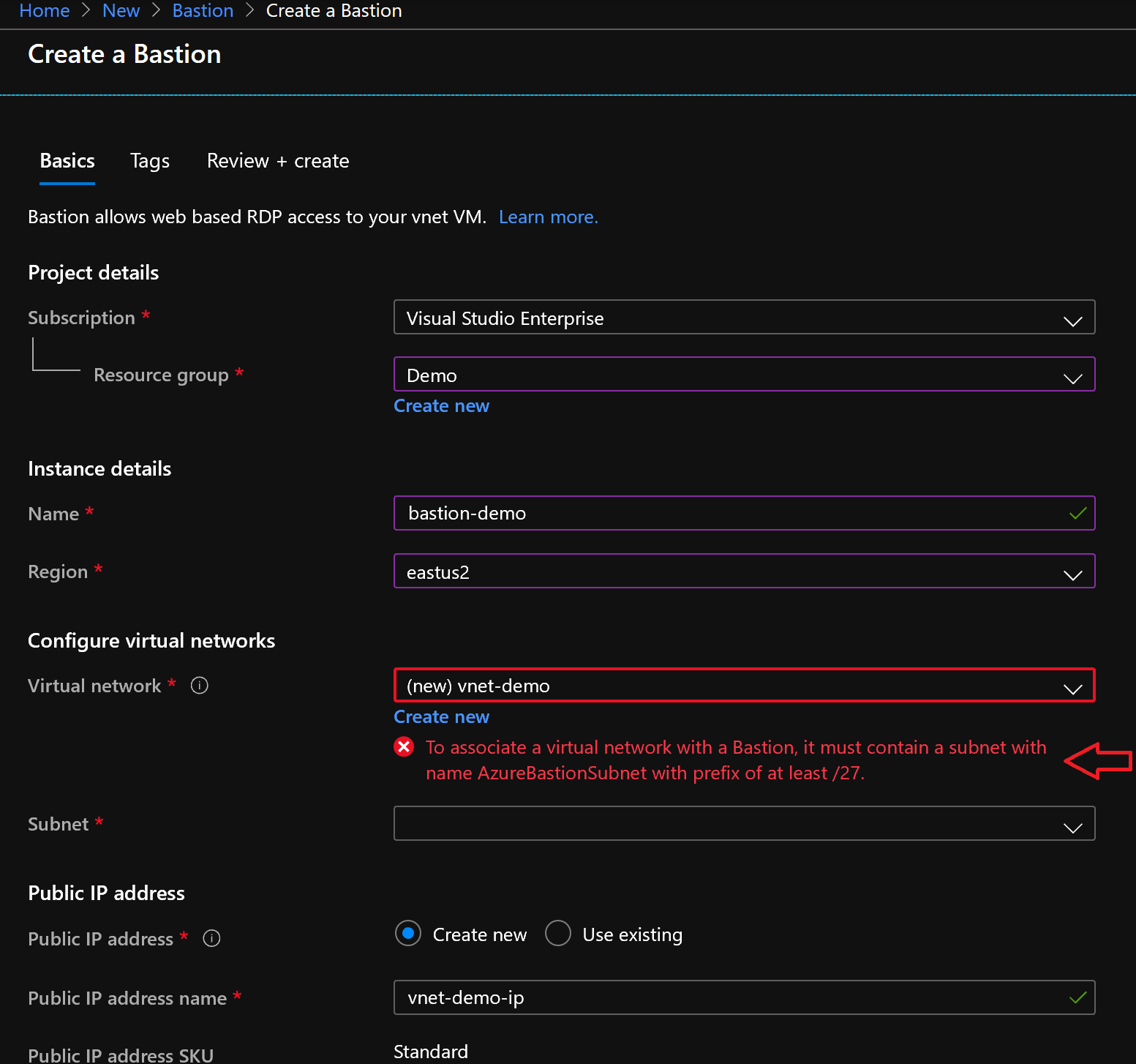
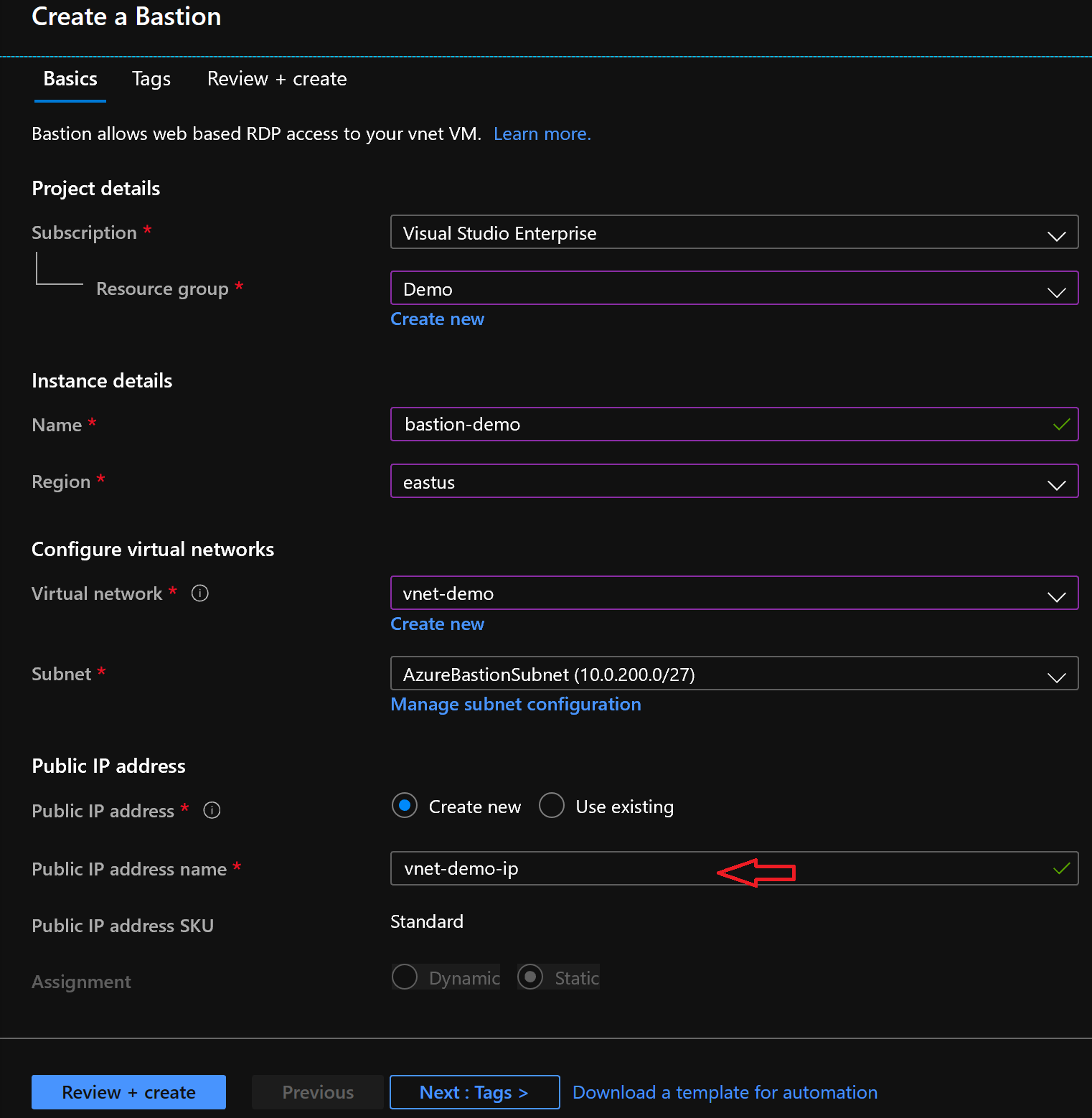
- Now choose a resource group to host the bastion resource, give it a name and pick a region (east-us for the demo). The Azure Bastion is deployed in a VNET, there is one-to-one relation between your VNETs, and your Azure bastion resources.
- We are using newly created VNET “vnet-demo” that is hosted for demo purpose. Please note that the wizard prompts to create a subnet in that VNET with an exact name of AzureBastionSubnet and with an IP prefix of at least /27.
- Create Subnet per requirements
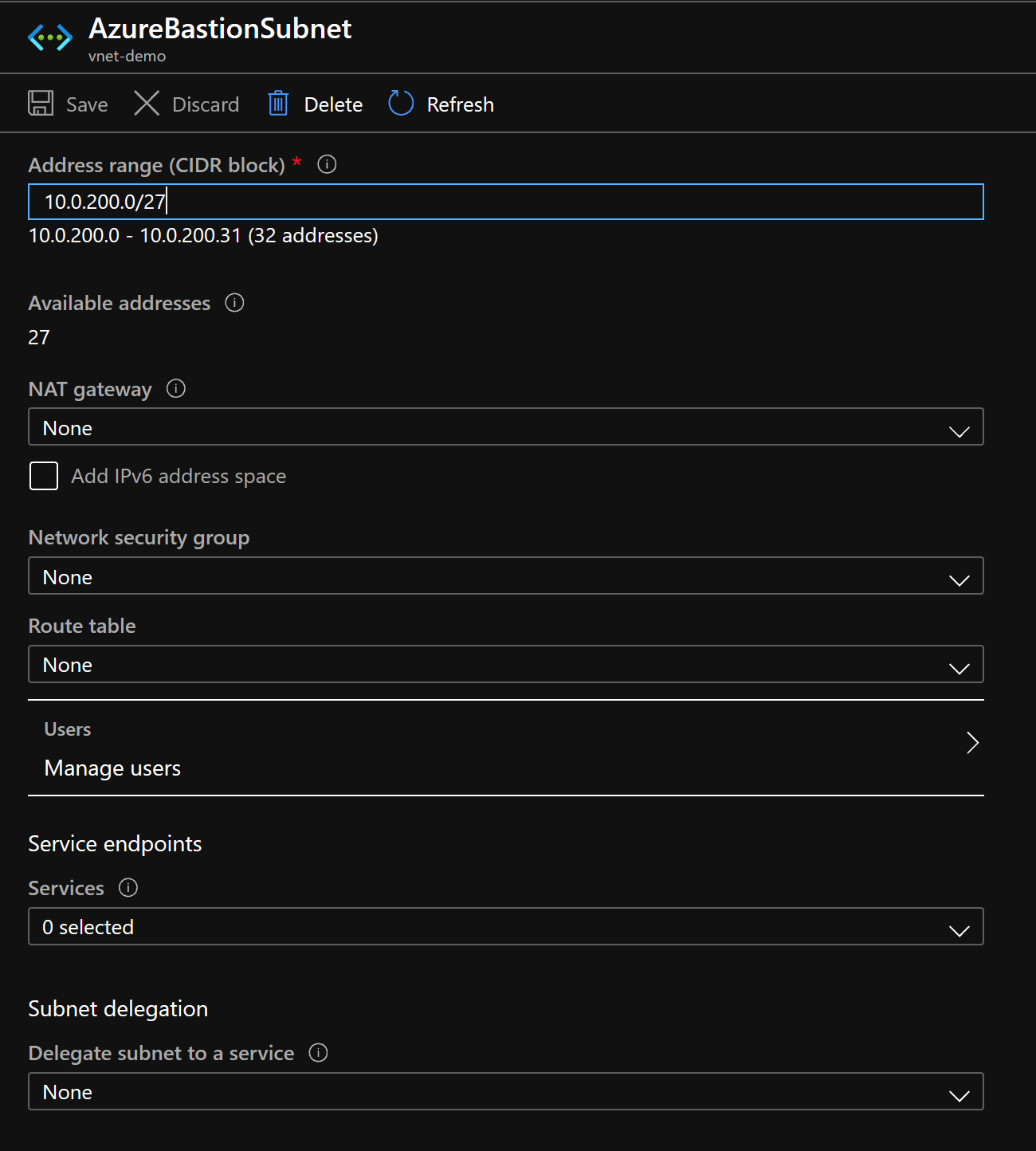
- Go back to the Azure Bastion deployment wizard and select the vnet and newly created subnet.
- Azure bastion host requires creating a public IP address that will be used for SSL connectivity only from the internet. Now this IP is not going to be attached to your VMs in anyway.
Azure automatically assigns a public IP to the service and generates a name that corresponds to the VNET declaration.
- Tagging: Don´t forget to assign tags for the service and all other resources, this helps you to get a well-defined Azure infrastructure.
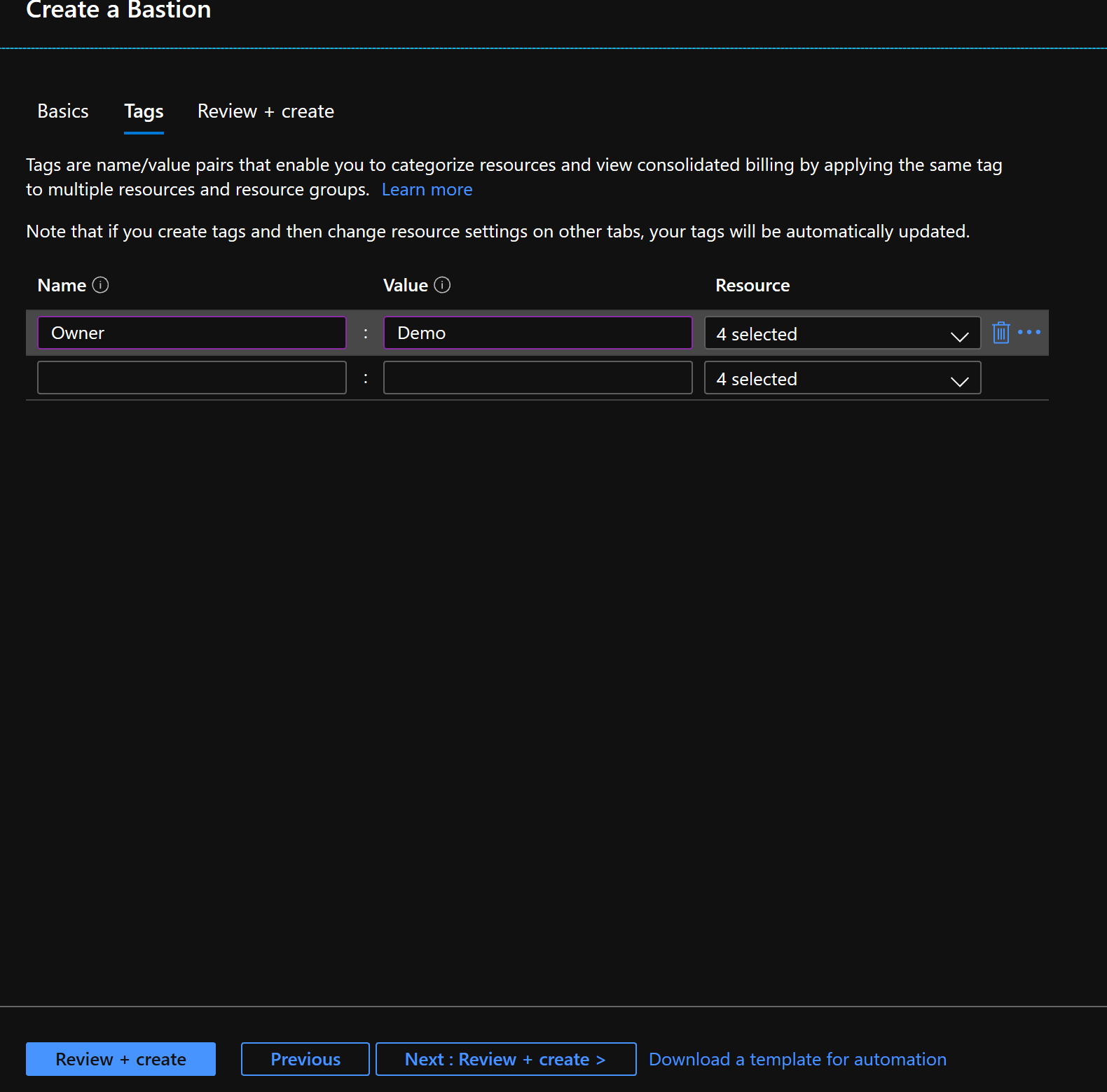
- Click “Review + create “. The service will be provisioned in your VNET.
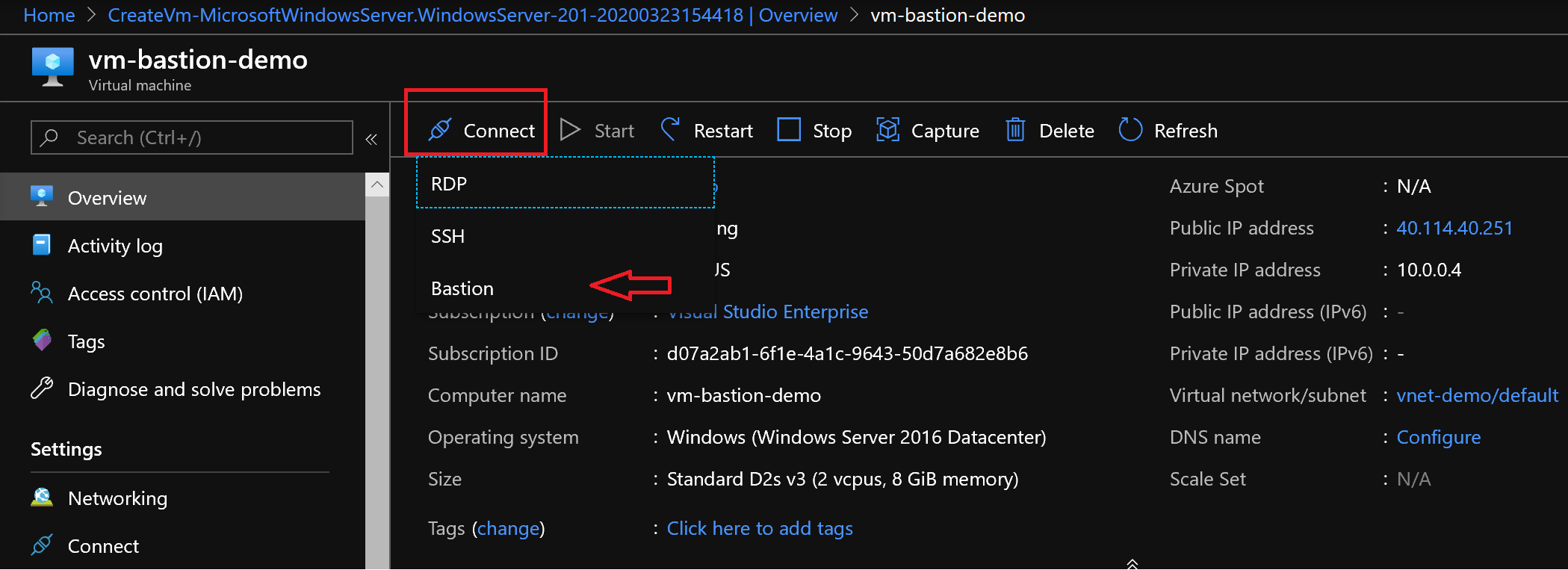
- Connect to a virtual machine: Select they virtual machine inside “vnet-demo” VNET.
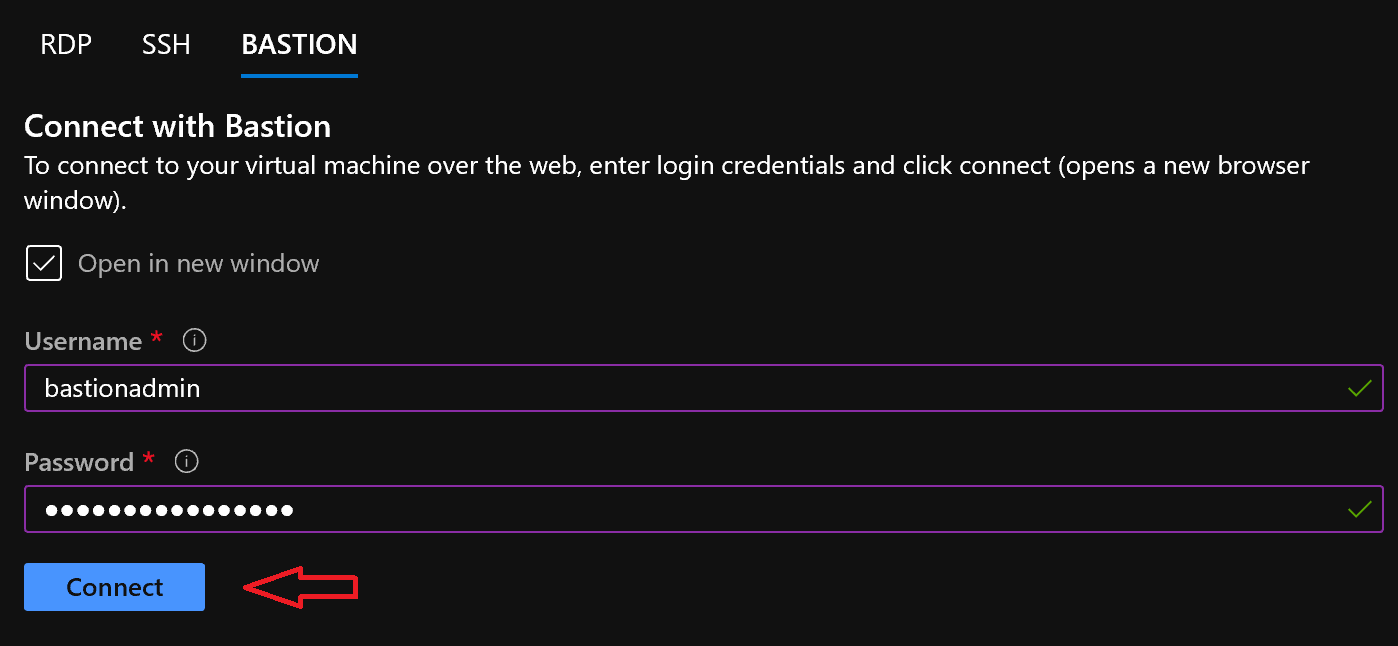
- Click “Connect” and you will see 3 options – RDP, SSH and Bastion.
Select “Bastion”.
- Enter the VM user credentials to connect to the VM and hit “Connect”
Security
Azure Bastion is a fully managed service by Microsoft and Microsoft hardens the service by default, but hardening to secure the Bastion host we should harden the subnet and use an NSG.
Create an NSG and define the following rules to the NSG,
- Allow 443 from service tag Internet
- Allow any traffic from a service tag called AzureCloud
- Allow any traffic from a service tag called Gateway manager.
References
You can learn more about Azure Bastion by referring to below mentioned Microsoft Documentation
https://azure.microsoft.com/en-us/services/azure-bastion/#overview
https://docs.microsoft.com/en-us/azure/bastion/bastion-overview
https://azure.microsoft.com/en-us/support/legal/sla/azure-bastion/v1_0/
https://docs.microsoft.com/en-us/azure/bastion/bastion-faq
https://azure.microsoft.com/en-us/updates/azure-bastion-is-now-available-in-20-new-regions/
https://azure.microsoft.com/en-us/pricing/details/azure-bastion/

0 comments