Today, we’re announcing the Microsoft Sentinel: NIST SP 800-53 Solution which enables compliance teams, architects, SecOps analysts, and consultants to understand their cloud security posture related to Special Publication (SP) 800-53 guidance issued by the National Institute of Standards and Technology (NIST).
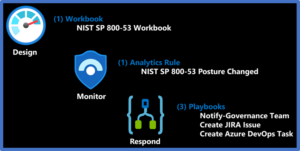
This workbook is designed to augment staffing through automation, visibility, assessment, monitoring, and remediation. Content features includes an intuitive user interface, policy-based assessments, control cards for guiding alignment with control requirements, alerting rules to monitor configuration drift, and playbook automations for response.
The resulting NIST SP 800-53 solution is a single pane of glass for gathering and managing data to address NIST SP 800-53 control requirements. The power of this solution lies in its ability to aggregate at big data scale across first- and third-party products to provide maximum visibility into cloud, hybrid, on-premises, and multi-cloud workloads.
What is NIST SP 800-53?
NIST SP 800-53 provides a catalog of security and privacy controls for federal information systems and organizations and a process for selecting controls to protect organizational operations. NIST SP 800-53 addresses a diverse set of security and privacy requirements across the federal government and critical infrastructure, derived from legislation, Executive Orders, policies, directives, regulations, standards, and/or mission/business needs. NIST SP 800-53 also sets the foundation for numerous compliance frameworks including Federal Information Security Modernization Act (FISMA), FedRAMP, NIST Cybersecurity Framework (CSF), and the Azure Security Benchmark. See NIST SP 800-53 for more information.
In this video, we demo and discuss the Microsoft Sentinel: NIST SP 800-53 Solution.
Solution benefits
- Design & build compliant architectures
- Quantifiable framework for measuring security maturity
- Monitoring & alerting of security posture, compliance drift, and blind spots
- Response via Security Orchestration Automation & Response (SOAR) playbooks
- Remediation with Cloud Security Posture Management (CSPM)
Solution content
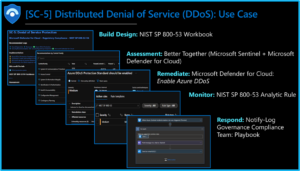
Microsoft Sentinel: NIST SP 800-53 Workbook: Provides a mechanism for viewing log queries, azure resource graph, and policies aligned to NIST SP 800-53 controls aggregated at big data scale across first- and third-party products to provide maximum visibility into cloud, hybrid, on-premises, and multi-cloud workloads. This workbook enables Security Architects, Engineers, SecOps Analysts, Managers, and IT Pros to gain situational awareness visibility for the security posture of cloud workloads. There are also recommendations for selecting, designing, deploying, and configuring Microsoft offerings for alignment with respective NIST SP 800-53 requirements and best practices.
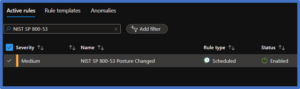
Microsoft Sentinel: NIST SP 800-53 analytics rule: This alert is designed to monitor Azure policies aligned to the NIST SP 800-53 Regulatory Compliance Initiative. The alert triggers if policy compliance falls below 70 percent within a 1-week timeframe. For more information, see the Microsoft Defender for Cloud: NIST SP 800-53 Rev. 4 Regulatory Compliance initiative.
Playbooks: Drive consistent and automation responses, ensuring security teams can focus their time on what’s important: providing remediation and response based on collected insights from Microsoft Sentinel, rather than navigating across portals for relevant data. Separation of duties is a central security requirement as security monitoring teams such as the Security Operations Center (SOC) often don’t have the respective security privileges to implement changes in the environment. Automations allow you to notify impacted teams of findings via email/Teams chat and documenting change requirements within IT service management tooling such as Azure DevOps and JIRA to ensure changes are implemented and documented within your configuration management requirements
- Notify governance compliance team: Notifies the governance compliance team of respective details via Teams chat and exchange email.
- Open DevOps task: Alert triggers an Azure DevOps task to address the Microsoft Defender for Cloud policy recommendations.
- Open JIRA ticket: Alert triggers a JIRA Ticket to address the Microsoft Defender for Cloud policy recommendations.
Getting started
Prerequisites
- Access Microsoft 365 Compliance Manager: Assessments
- Onboard Microsoft Sentinel
- Onboard Microsoft Defender for Cloud
- Add the Microsoft Defender for Cloud: NIST SP 800-53 R4 & R5 Assessments to Your Dashboard
- Continuously Export Security Center Data to Log Analytics Workspace
- Extend Microsoft Sentinel Across Workspaces and Tenants
- Configure Auto Provisioning of Microsoft Defender for Cloud Agents
- Review Microsoft Service Trust Portal
Deployment
- Microsoft Sentinel > Content Hub > Search “NIST SP 800-53” > Install > Create > Configure Options > Review + Create
- Review Content
- Microsoft Sentinel > Workbooks > Search “NIST SP 800-53”
- Microsoft Sentinel > Analytics > Search “NIST SP 800-53”
- Microsoft Sentinel > Automation > Active Playbooks > Search “Notify-GovernanceComplianceTeam”, “Open-JIRA-Ticket”, “Create Azure DevOps Task”
- Review: ReadMe for additional Getting Started requirements.
- Feedback: Let us know what you think in the survey
Print/export report
- Open NIST SP 800-53 Workbook > Select Subscriptions/Workspaces/Time > Select Options > Workbook prints what’s visible for custom reporting requirements
- Set Background Theme: Settings > Appearance > Theme: Azure > Apply
- Print/Export Report: More Content Actions (…) > Print Content
- Settings: Layout (Landscape), Pages (All), Print (One Sided), Scale (60), Pages Per Sheet (1), Quality (1,200 DPI), Margins (None) > Print
- Executive Summary: Microsoft Defender for Cloud > Regulatory Compliance > Download Report > Report Standard (NIST SP 800-53), Format (PDF)
Use case example
Frequently asked questions
- Are additional products required?
- No, this solution leverages your existing Microsoft Security architecture. The recommended products provide additional use case enrichments, but only Microsoft Sentinel and Microsoft Defender for Cloud are required to get started.
- Are multi-subscription, multi-cloud & multi-tenant supported?
- Yes, via Workbook Parameters, Azure Lighthouse, and Azure Arc
- Are third-party products supported?
- Yes, via Microsoft Sentinel Incidents aggregation of alerting.
- Is custom reporting available?
- Yes, via guide, time, workspace, & subscription parameters.
- Is this available in government regions?
- Yes, this solution is deployable to all clouds
- Are blank panels bad?
- No, they’re an opportunity to explore/address the requirements
- Can this content be exported as a report?
- Yes, via Print Workbooks and Download Artifacts
Learn more about NIST SP 800-53 with Microsoft Security
- National Institute of Standards and Technology (NIST) SP 800-53
- NIST SP 800-53 Rev. 4 Regulatory Compliance built-in initiative
- Microsoft Cloud Service Trust Portal
Each control below is associated with one or more Azure Policy definitions. These policies may help you Assess Compliance with the control; however, there often is not a one-to-one or complete match between a control and one or more policies. As such, Compliant in Azure Policy refers only to the policy definitions themselves; this doesn’t ensure you’re fully compliant with all requirements of a control. In addition, the compliance standard includes controls that aren’t addressed by any Azure Policy definitions at this time. Therefore, compliance in Azure Policy is only a partial view of your overall compliance status. The associations between compliance domains, controls, and Azure Policy definitions for this compliance standard may change over time.
Customer experience will vary by user and some panels may require additional configurations for operation. Recommendations do not imply coverage of respective controls as they are often one of several courses of action for approaching requirements which is unique to each customer. Recommendations should be considered a starting point for planning full or partial coverage of respective requirements. This workbook does not address all controls within the framework. It should be considered a supplemental tool to gain visibility of technical controls within cloud, multi-cloud, and hybrid networks. For the full listing of respective controls, see the Microsoft Cloud Service Trust Portal.



Excellent