A lot of hard work goes into the planning and preparation for Ignite, but we’re always excited to showcase the progress we’ve made towards meeting our developer community’s needs and our company’s vision. The tools, capabilities and features we’re announcing this year support each. Our ambition to extend Microsoft Graph to include customers’ data is now turning into action. We’ve delivered new SDKs and tools to help our developer community create richer, more powerful cross-platform experiences. Of course, we’re also continuing the good work of consolidating our API surface area and capabilities behind the unified endpoint. What follows is a more detailed look at our efforts.
Bringing data into Microsoft Graph
For some time, we’ve heard developers and customers ask if they can bring their files and custom data types into Microsoft Graph to take advantage of our first-party experiences, and in particular, search. This week at Ignite, we’re announcing the preview of six Microsoft-built connectors, over one hundred thirty connectors from ecosystem partners and new indexing APIs that allow you to build your own connectors and index your data to participate in Microsoft Search. We’re also expanding the preview of our Microsoft Graph search API to give a broader audience the chance to start “kicking the tires” on developing connectors and on developing custom search applications. Get more information at https://aka.ms/iwantconnectors.
Another common request is for the ability to extend user data in Microsoft Graph to include similar data – for example, certifications or language skills – from other systems of record. We’re pleased to announce the public preview of over a dozen new or extended user profile entities on the profile API that make it possible to bring richer profile information into the context of the profile card in Microsoft 365.
New integrations make it easier than ever for developers to leverage data and insights from the Microsoft Graph Security APIs in their other security toolsets. RSA Netwitness, ServiceNow and Splunk now offer integrations with Microsoft Graph Security API alerts. We also extended support for sending customer threat intelligence to Microsoft services via Microsoft Graph Security API threat indicators. Now, in addition to Azure Sentinel, customers can send indicators to Microsoft Defender ATP to block or alert on threats using their own intelligence sources. Integrations with partners like ThreatConnect enable customers to send indicators directly from threat intelligence and automation solutions. Finally, support for new triggers was added to the Microsoft Graph Security API Logic Apps and Flow connectors and sample playbooks. Read the Microsoft Graph Security API blog post for details on all of these and more.
Investing in the developer experience
Assisting and accelerating cross-platform development on Microsoft Graph is a priority, and we’ve invested in the creation of several new SDKs. Developers and IT pros want better tools to iterate through tenant data – for example, to manage users or report on group membership and ownership. We’re happy to announce the preview of our new Microsoft Graph PowerShell SDK. In addition to this SDK, developers working with our notifications API to enable push user-centric notification experiences can now use our new suite of specifically tailored lightweight SDKs for Windows, Android, iOS, and JavaScript. These new SDKs have smaller footprints, an improved authentication model, and support for web apps using web push.
In addition to producing new SDKs, we are building chaos handlers (AKA “Chaos Giraffe”) to help developers interactively verify that their applications are resilient to server failures that are tricky to initiate. Chaos handlers can easily be inserted into existing applications and can randomly or predictably generate failures such as 429 (Too Many Requests) or (503 Server Unavailable) errors.
Developers and data scientists working with Microsoft Graph data connect now have access to generally available tools that translate Office 365 data into Common Data Model format, making it schematically consistent with other Open Data Initiative (ODI)-ready datasets.
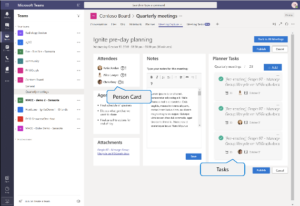
Microsoft Graph Toolkit, a collection of framework-agnostic web components powered by Microsoft Graph, is now generally available and available on GitHub. With just a few lines of code, a developer can insert common elements like agendas, tasks, person cards, and people cards into an app, saving real development time. The toolkit components are also customizable, making it possible to tailor the look and feel of just about any experience. The following are some examples of how toolkit components show up in a reference solution app we recently built.
Microsoft Graph Toolkit: examples
 |
 |
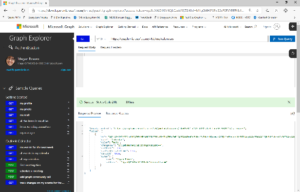
Last but certainly not least, we’re pleased to introduce a new preview version of one of our most popular tools, Graph Explorer. It has a new look and feel, but and more importantly, queries in the new Graph Explorer Preview are returned with useful contextual information like permissions, access tokens, and SDK code snippets, that was previously only discoverable in the documentation. On the current Graph Explorer, users will find a toggle button under the “Sign In with Microsoft” button that enables them to switch between versions and try out the preview. If you’d like to give us feedback, drop us a line on User Voice.
| Graph Explorer | Graph Explorer Preview |
 |
 |
Enhancing our capabilities
We continue to consolidate our Microsoft 365 API surface area around Microsoft Graph. The Identity team continues to make strides toward parity with the Azure AD Graph with the addition of the application API to the production endpoint. A range of password management capabilities requested through User Voice, including methods for adding and removing passwords and managing password changes, are now generally available. Retrieval of a user’s last sign-in time and B2C provisioning management are now available in preview.
The explosive growth in Microsoft Teams adoption is echoed by demands from the developer community. The community is eager to create and manage highly customized workspace solutions and to accelerate solution adoption.
We are previewing two significant new capabilities – a webhook API that provides notifications that include chatMessage changes – including deletion – to facilitate several in-demand scenarios, including compliance and workflow management, and resource-specific consent. Resource-specific consent is designed to alleviate concerns we’ve heard from IT administrators about Group.ReadWrite.All scenarios associated with third-party solutions. This capability constrains an app’s access to only certain groups – a win for admins, users, and developers! We expect to roll out resource-specific consent more broadly across the Microsoft 365 platform in the future.
With resource-specific consent putting additional emphasis and dependencies on groups, we’ve shipped new capabilities to dynamically evaluate group membership, and to enable renewal and expiration times on group entities.
The Intune endpoint continues to expand. The Intune team is previewing support for adding and enrolling Windows, Apple, and Android devices, more options for managing security baselines and policy groups and sets, and finally, support for app-only permissions for read/write operations.
In both Outlook Mail and calendar, we’re making a set of highly anticipated capabilities generally available on the Microsoft Graph endpoint, like getting MIME-formatted messages and attachments, and support for large email attachments. In addition, developers can now get and set the user’s preferred date and time formats in mailboxSettings. Developers working with the Microsoft Graph calendar APIs will find a set of very useful new entities for managing events and mailbox settings. And in late-breaking, hot-off-the-press news, we’ve updated the Places API preview so that developers can use the Graph API to set metadata for rooms instead of relying on external APIs created built by 3rd parties. We’ll update the blog to include a link to the documentation in the coming days.
Wrapping up
Whether or not you’re joining us at Ignite, we hope you’ve enjoyed this summary of Microsoft Graph news. If you’re in Orlando, we’d love to see you at our sessions or to meet you in the Microsoft 365 Developer Platform area in the Hub. If you can’t make it to Ignite this year, join us virtually through Tech Community or at one of the thirty-one Ignite Tour cities we’ll visit this year. And of course, you can always reach us with suggestions or features requests on UserVoice, see what we’re sharing on GitHub, or post questions on StackOverflow.
Happy coding.
The Microsoft Graph team

0 comments