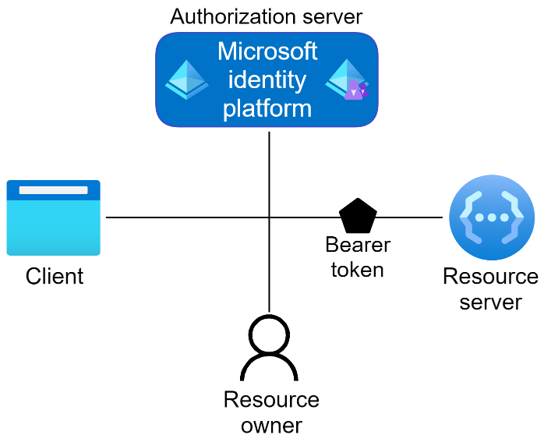
We are pleased to announce official .NET MAUI support in Microsoft.Identity.Client 4.47.0 to easily add authentication into your apps. In this blog we will take a look at how to perform authentication in .NET MAUI apps to acquire the desired token.
Commonly authentication is done in three ways:
- Basic – This is used when authentication is done for both personal and corporate accounts without using a broker (or Authenticator). For clarity, personal account mean Microsoft personal account such as Outlook, Hotmail etc.
- With Broker – This is intended for corporate accounts where an extra layer of security is added by using Authenticator/Broker. This is useful for MFA and is required to comply with other security policies such as conditional access.
-
B2C – This is used when the end user is allowed to login using OAuth2 credentials such as Google, Facebook etc. This does not support broker.
We provided one sample for each type Samples.
All the samples use the standard Acquire Token Silent (ATS) + Acquire Token Interactive (ATI) flow i.e. app attempts to acquire token silently and if that fails, it invokes UI to acquire it interactively. The token is then used to retrieve data from the backend.
The apps have a wrapper
PCAWrapper(B2C)for MSAL client. The wrapper implements singleton pattern. WhenPCAWrapperis instantiated, it builds PublicClientApplication using the preconfigured values. It also provides logging support. It separates the UI code cleanly from UI by wrapping MSAL related error handling, constants, and other parameters.Platform specific code and configuration is in the corresponding subfolders inside Platforms folder. These sample apps can run as they are on iOS, Android, and Windows platforms. When you create your own App, you need to configure it in the Azure portal and replace the values. The instructions to register your App are How to register.
Basic
The Basic App demonstrates the use of authentication for both personal and corporate accounts. This app shows the use of both embedded and system browsers. We strongly recommend using System browser as it stores the usernames and passwords for the user.
You can run the app as it is or create your own app and register as mentioned above.
When user clicks the SignIn button, it will set the flag to use system or embedded browser in the PCAWrapper and call AcquireTokenSilentAsync.
PCAWrapper will attempt to acquire token silently for the first account and return the result. If UI is required, MSAL.NET throws MsalUiRequiredException.
If app gets the result, it is used to obtain information from MSGraph service.
App catches the exception and invokes AcquireTokenInteractiveAsync method of PCAWrapper. PCAWrapper will use the embedded flag and the parent window set by platform specific code to display the Ux. User can securely enter the username and the password. These are transparent to the app and go directly to the backend. Upon completion, it will return the authentication result to the app.
Broker
This app is very similar to the Basic app with the following changes:
- The interactive UI is invoked exclusively using broker
- It does not support embedded view functionality.
In case you are wondering why does AcquireTokenInteractive still calls WithParentActivityOrWindow if it is using broker, it is used as a backup mechanism if user has not installed the broker.
B2C
B2C app needs to be registered in the Azure portal in a different way. Registration is explained in this Tutorial.
The UI flow and the structure of the App is same as other apps with the following differences:
- The app retrieves the claims from the
ClaimsPrinciplalinstead of calling the backend API. - The wrapper must pass the B2CAuthority during creation and while acquiring token silently.
MSAL.NET in Action
Want to learn more about MSAL.NET and .NET MAUI? Checkout my session from the recent .NET Conf: Focus on MAUI event:
Summary
Here are resources to get you started.
- NuGet package for MSAL.NET.
- MSAL samples for .NET MAUI
- MSAL.NET GitHub repository.
- App Types and Auth Flows
- .NET Conference Video
If you have any questions or concerns, please raise issues on the GitHub.


Everything I’ve found has the msal data scheme hard coded in the app. Would there be a reason to keep it secure? And how would you do that?
Using the sample Code for the MauiAppWithBroker. I have modified the ClientID, TenantID, AndriodRedirectURI to My test AzureAD stuff. The code does not get passed AuthenticationResult result = await PCAWrapper.Instance.AcquireTokenInteractiveAsync(AppConstants.Scopes).ConfigureAwait(false); line of code. The browser gets stuck “Are you trying to sign in to {your appname};
I would also like to use Graph too.
A readme file would be great to know all the variables that need to change.
Thanks for all your help
Great work….
How BlazorWebView accesses extended stored images .
This information is very useful.
One criticism I have of this library is that it requires too much programming for the SDK to get things to work.
It seems to me that the setup uses too much boiler plate code which I find to be cumbersome and invasive. It's very frustrating because the setup for Blazor (server side specifically) is much cleaner and doesn't require a lot of added setup in an application's startup. Case in point, we have an on-premises Blazor website that uses Azure AD to login, and it is a great user experience and doesn't require much maintenance for logins.
However, when we decided...
Good information, but how can I use the GraphClient
initialize for .Net Maui Android? Everything I tested
didn’t work.
Thanks for the feedback about the GraphClient. One more person is asking for the same. I will look into it. What did not work? Can you please provide more specifics? If you have issues in the samples, it will be good to have the specifics on the GitHub as issues. So, it is closer to the code and can be tracked as issue. Thx.
Would be nice if you also showed how to hook it up to the GraphClient (which is used for OneDrive and other office 365 services)
I made my own workaround for it, but if there’s a cleaner way please show us
As the Azure Identity library’s Authenticator, that’s used by it but,does not have the with parent or activity function, and does not work with Maui android.
Thanks for the feedback about the GraphClient.
Praise your work.