The Azure Networking team has announced the general availability of Virtual Network (VNet) Service Endpoints for Azure SQL Database in all Azure regions, including Azure Government. The announcement can be seen here: VNet Service Endpoints for Azure SQL Database now generally available
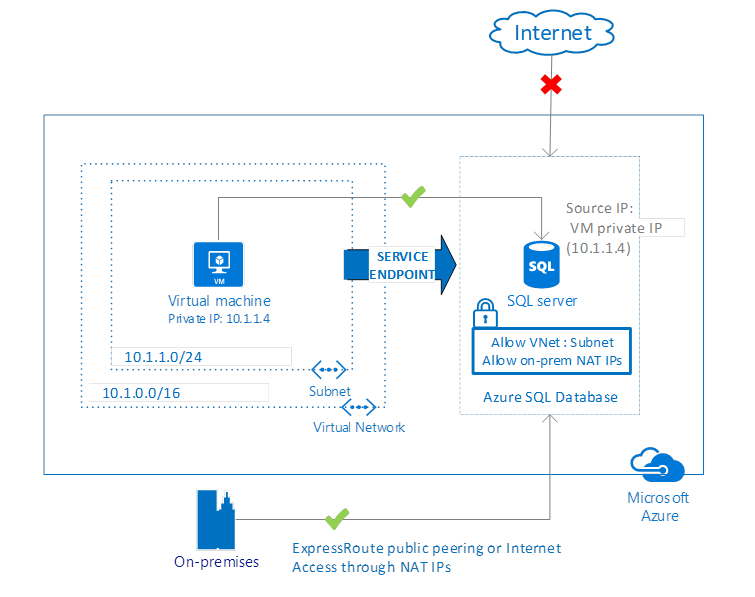
VNet Service Endpoints for Azure SQL Database allow customers to isolate connectivity to their logical server from only a select subnet or subnets within their VNet. This enhances both security and performance by extending your VNet private IP space and identity directly to Azure SQL Database without leaving the Azure Government data center infrastructure. This allows customers to secure critical database resources to only their virtual networks, providing private connectivity to these resources and removing dependencies on Internet facing public IP addresses. Azure Government ExpressRoute customers who are required to route VNet traffic back to on-premise before accessing Internet facing services can also expect to see performance improvements when accessing Azure SQL Database. Virtual machines in private VNets will now be able to reach database resources directly without the need to hairpin traffic on-premise to Public/Microsoft peering or to the Internet.
Next Steps
To get started, refer to the documentation Virtual Network Service Endpoints and VNet Service Endpoints and rules for Azure SQL Database.
For feature details and scenarios please watch the Microsoft Ignite session, Network security for applications in Azure.

0 comments