Did you know that starting with Android 9 (API level 28) cleartext(non-HTTPS) support is disabled by default? It is always recommended to make connections over HTTPS to ensure that any web communication is secure. This policy may have an impact on your development cycle if your app needs to download an image or file on a server hasn’t been configured for HTTPS. Also, you may just be trying to debug your application locally and don’t want to install development certs. You may have strong business requirements that all web traffic on all versions of Android is always HTTPS. This is where the new Network Security Configuration feature of Android comes in, to help us finely tune network traffic security in our app.
When does Cleartext apply?
Cleartext is disabled by default on Android 9 (Pie, API 28) devices when your application is set to target and compile against Android 9. On the project’s properties you will find the SDK you are compiling against under Application:
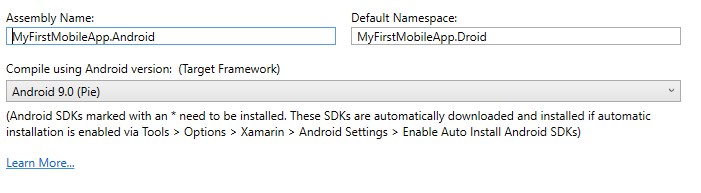
Inside of your Android Manifest options you will find the Target Framework that can be set to Android 9:
Network Security Config
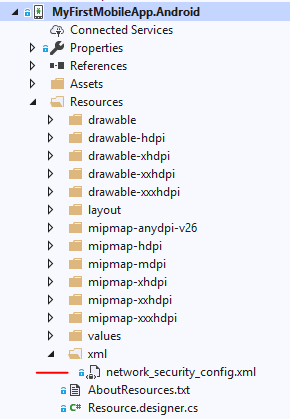
To configure security options, you will create a new xml file under Resources/xml named network_security_config.xml.
The following configuration will enable cleartext web traffic to be allowed in our app for specific domains and IP addresses:
<?xml version="1.0" encoding="utf-8"?>
<network-security-config>
<domain-config cleartextTrafficPermitted="true">
<domain includeSubdomains="true">10.0.2.2</domain> <!-- Debug port -->
<domain includeSubdomains="true">xamarin.com</domain>
</domain-config>
</network-security-config>
You can strengthen the security of your app by also restricting cleartext traffic on all versions of Android regardless of the compile and target framework. This is accomplished by setting cleartextTrafficPermitted to false. Enabling this will restrict any traffic that is non-HTTPS at all times.
Configure Application Manifest
The last thing that needs to be done is to configure the networkSecurityConfig property on the application node in the Android Manifest:
<?xml version="1.0" encoding="utf-8"?>
<manifest>
<application android:networkSecurityConfig="@xml/network_security_config">
...
</application>
</manifest>
That’s it! Now the application is completely configured to allow or restrict cleartext during web requests.
Learn More
Network security configuration can do a lot more than just allow or restrict cleartext traffic in Android applications. It can configure trust anchors, debug-only overrides, certificate pinning, and more. Be sure to read through the Android developers documentation for a full guide. To enable cleartext traffic in iOS applications, you will want to take a look at our App Transport Security(ATS) documentation for a full walkthrough.

hello, why do you keep giving me this error and don’t go on? thanks
“Using Network Security Config from resource network_security_config debugBuild: true”
my code :
network-security-config
domain-config cleartextTrafficPermitted=”true”
domain includeSubdomains=”true”>127.0.0.1 /domain
domain includeSubdomains=”true”>line-me.app /domain
/domain-config>
/network-security-config
Hello
I came to your blog after searching on how to deal with cleartext_not_permitted.
I have an app which loading pages from local so there is no SSL.
The IP and the port is not the same everytime and it depends on the user.
So i tried your solution but what if you don’t know the IP and the port?
What we have to write to the config file?
Thanks
You should just be able to leave it empty and it would be all domains from my understanding: https://developer.android.com/training/articles/security-config
Basically: cleartextTrafficPermitted=”true”
Leave WHAT empty exactly? Because if you don't specify a domain to allow you get this error:
{Java.Lang.RuntimeException: Failed to parse XML configuration from network_security_config ---> Java.Lang.Exception: No domain elements in domain-config at: Binary XML file line #1
I think in your last post you were straight guessing. As far as I can tell what you have documented does NOT work. No matter what I try I get the clear text error. I've spent two days trying everything under the sun. It's like Google thinks were too stupid to know to use SSL when deploying so they've made it...
Does this require any specific version of the Xamarin tools to work?
I added a network_security_config file, and added it to the manifest. However, after that change the call to LoadApplication (Xamarin.Forms.Platform.Android.FormsAppCompatActivity.LoadApplication) on app startup throws a null reference exception:
[0:] System.NullReferenceException: Object reference not set to an instance of an object.
at Xamarin.Forms.Platform.Android.FormsAppCompatActivity.InternalSetPage (Xamarin.Forms.Page page) [0x0005e] in D:\agent_work\1\s\Xamarin.Forms.Platform.Android\AppCompat\FormsAppCompatActivity.cs:315
at Xamarin.Forms.Platform.Android.FormsAppCompatActivity.SetMainPage () [0x00000] in D:\agent_work\1\s\Xamarin.Forms.Platform.Android\AppCompat\FormsAppCompatActivity.cs:343
at Xamarin.Forms.Platform.Android.FormsAppCompatActivity.LoadApplication (Xamarin.Forms.Application application) [0x0025c] in D:\agent_work\1\s\Xamarin.Forms.Platform.Android\AppCompat\FormsAppCompatActivity.cs:139
at SomeApp.MainActivity.OnCreate (Android.OS.Bundle savedInstanceState) [0x001db] in D:\work\xxx\MainActivity.cs:173
Hmmm, that looks like something else. You would need to compile against Android 9.0. This wont have any impact on Xamarin.Forms itself as they are completely separate. Perhaps look at some other change that was made to the code.
Hi, Nice tutorial. Did anything change meanwhile? I am trying to connect to a 10.0.2.2 but I still get the cleartext error. I am sure I achieved this before but can’t remember if I followed here or somewhere else. I would really appreciate your help.
Very usefull. Thanks
Hi, james I can’t find the androidManifest.xml file, where i can find it??
You can see it in the Android project, inside to “Properties”.
https://www.screencast.com/t/V5oEfUBDOc
Hi, James how do you deal with this when you are on an internal 192.168.0.13:8080 I am not on a domain so what would my value be in this case that goes in the XML file. Lest android is getting tougher on security makes sense.
Yup, you would put the IP address inside of the file.
The hyperlink to Android developers documentation page is not working (404).
Thanks for pointing it out 🙁 looks like Google broke their link, but here is the cached version: https://webcache.googleusercontent.com/search?q=cache:hOONLxvMTwYJ:https://developer.android.com/training/articles/security-config+&cd=10&hl=en&ct=clnk&gl=us