Government agencies have an increased need for secure, verifiable, and compliant cloud environments that adhere to data sovereignty regulations, operate in a Zero Trust framework, and help reduce exposure to insider threats.
Today, Microsoft marks a major milestone in secure cloud innovation with the general availability of Azure Confidential Computing (ACC) for Secure Encrypted Virtualization – Secure Nested Paging (AMD SEV-SNP) based virtual machines across all U.S. government data classification levels. ACC VMs help protect sensitive workloads by using hardware-backed Trusted Execution Environments (TEEs) to safeguard data while it is in use, along with attestation capabilities that help customers verify the environment their workloads are running in. This release follows the recent general availability of confidential VMs in commercial Azure and extends those capabilities to government customers.
What is confidential computing?
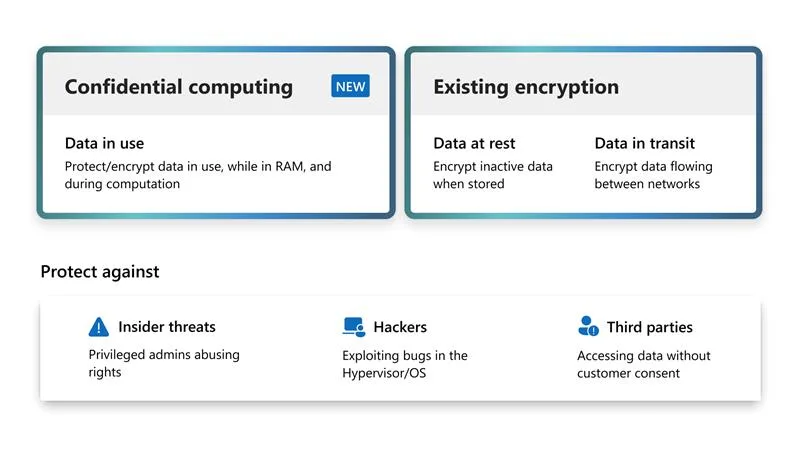
Confidential computing is a transformative approach to cloud security. It helps protect data not only when it is stored or transmitted, but also when it is being processed. This is achieved through a Trusted Execution Environment (TEE), which is an isolated area within the processor designed to keep code and data shielded from unauthorized access, including from higher-privileged software layers.
How does this help our U.S. government customers?
For many government workloads, the challenge of cloud security is not only protecting data at rest and in transit. It is also reducing risk while data is actively processed. Confidential VMs help address this by providing hardware-based isolation and cryptographic attestation, so customers can add additional assurances for confidentiality and integrity.
For government agencies, this can help you:
- Reduce exposure to privileged access by helping keep sensitive code and data protected within the TEE while it is in use.
- Enable additional cloud adoption scenarios by supporting sensitive processing that previously required on-premises isolation.
- Improve operational efficiency by consolidating infrastructure while maintaining additional protections for sensitive workloads.
- Increase transparency by validating platform integrity signals, which can strengthen trust in the cloud environment.
- Verify runtime environments independently using cryptographic attestation services such as Secure Key Release (SKR), which can help confirm that the VM is running on attested, confidential hardware.
These capabilities are designed for workloads that require strong confidentiality and integrity assurances, including sensitive mission and regulated scenarios.
In Summary
Azure Confidential Computing makes it possible for government agencies to migrate their most sensitive workloads to the cloud with their unique operational requirements in mind.
To get started with Azure Confidential Computing (ACC) virtual machines in U.S. government environments, review the Azure Confidential Computing documentation for supported VM sizes and deployment guidance. You can then create a confidential VM in the Azure portal when it is available in your region.
We will continue to expand Azure Government capabilities that help customers run sensitive workloads with stronger security assurances. Watch this blog for future updates.

0 comments
Be the first to start the discussion.