If you use build service identities like Project Collection Build Service to call Advanced Security APIs, the Advanced Security permission changes in Sprint 269 broke that. We restricted API access for build identities as a security improvement but failed to provide an early notice for customers that relied upon this for various automations.
We’re rolling it back temporarily. The restriction will be re-enforced on April 15, 2026.
What you should do
Action is required. The recommended path is a service principal with Advanced Security: Read alerts permissions for your Advanced Security-enabled repositories. Scope it narrowly, and if the service principal isn’t committing code, it won’t consume an Advanced Security committer license.
Status checks in Sprint 272
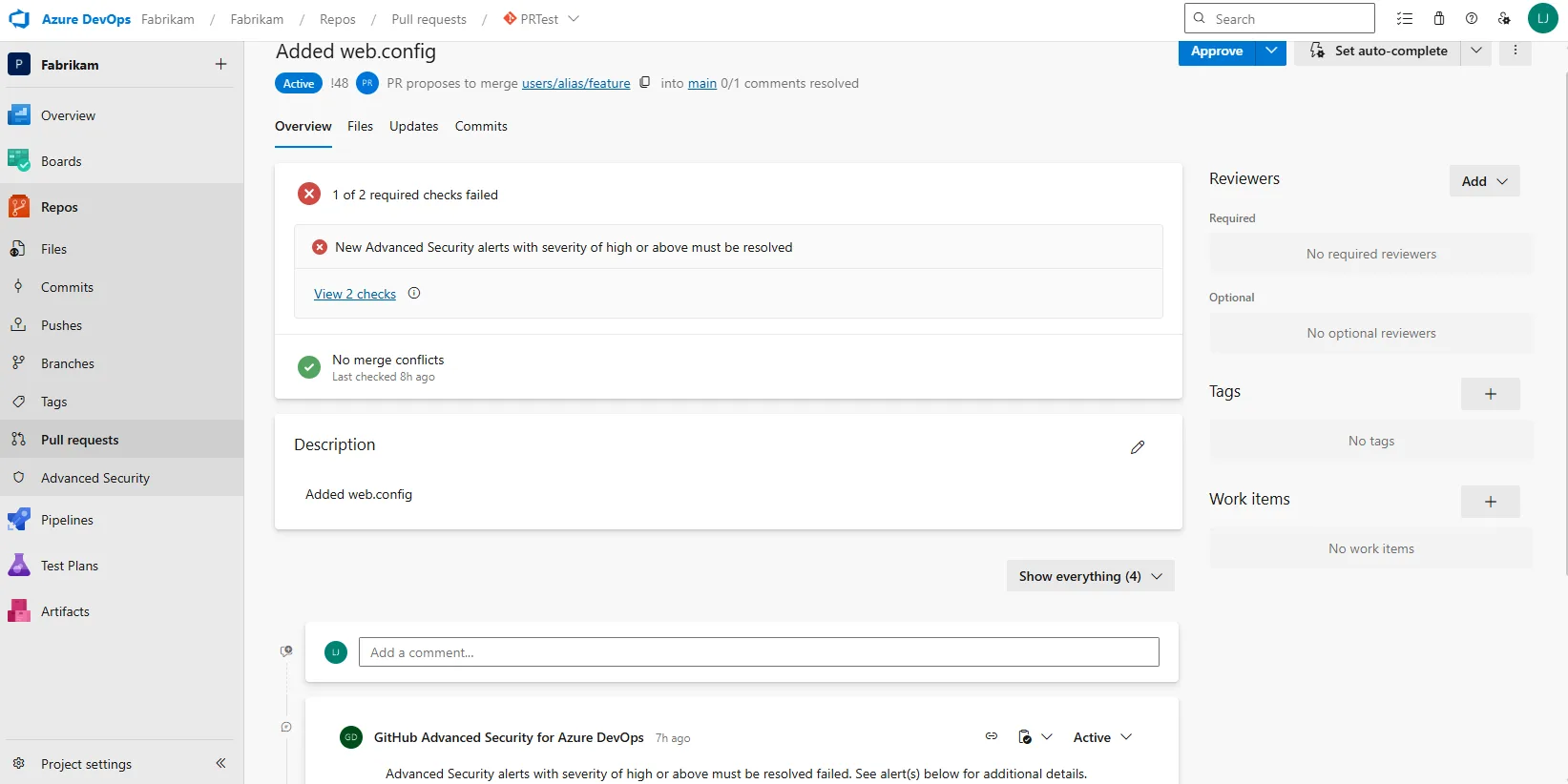
We’re also shipping status checks soon, which give teams a native way to gate on security posture without API-driven alert mutations from pipeline identities.
This won’t replace every automation scenario, though it enables pull request-time blocking on the presence of high and critical alerts.
Have feedback or hitting gaps moving to a service principal? Let us know.
Action required by April 15: move API automation to a service principal with Advanced Security: Read alerts or watch for status checks in Sprint 272.

0 comments
Be the first to start the discussion.