Auditing is important in any environment and solution, to get a view on who is doing what, typically from a compliance or governance perspective. In most scenarios, the solution allows you to store auditing to a logfile. The downside is that nobody is really watching over the logs, until something goes wrong.
Auditing is enabled by default for all Azure DevOps organizations, and cannot be turned off. This guarantees that you never miss an actionable event. Events get stored for 90 days after which they will get deleted automatically. One possibility though is, you can back up audit events to an external location to keep the data for longer than the 90-day period.
The scenario I talk about in this article, is optimizing Audit Logging within Azure DevOps, by enabling the new, currently in public preview, ADO Audit Stream.
What/Why ADO Audit Stream
Instead of using the built-in Audit Logging, which allows DevOps Project Admins to retrieve Audit logging on screen, validate the activities happening in the Azure DevOps organization and optionally exporting to a JSON- or CSV-file type logfile, ADO Audit Stream allows for more transactional streaming of auditing information.
By deploying an audit stream, auditing data can get sent to other services or solutions outside of Azure DevOps for further processing or inspection. Sending auditing data to other Security Incident and Event Management (SIEM) tools opens possibilities, such as alerting on specific auditing events, creating views on auditing data, and performing anomaly detection. It also allows you to store more than the default (and fixed) 90-days retention of auditing data.
Audit streams represent a continuous stream of auditing logging events from your Azure DevOps organization to a stream target. Every half hour or less, new audit events are bundled and streamed to your targets. Remember that Audit Stream is an Organization setting, capturing all audit events from all projects within Azure DevOps.
For now – remember it is in Public Preview so features might still change – Audit Stream supports 3 different scenarios as Stream Targets:
a) Azure Event Grid b) Azure Monitor Logs c) Splunk
Scenario
In this article, I focus on Azure Event Grid integration only, to give you some idea about the concept of Auditing Stream
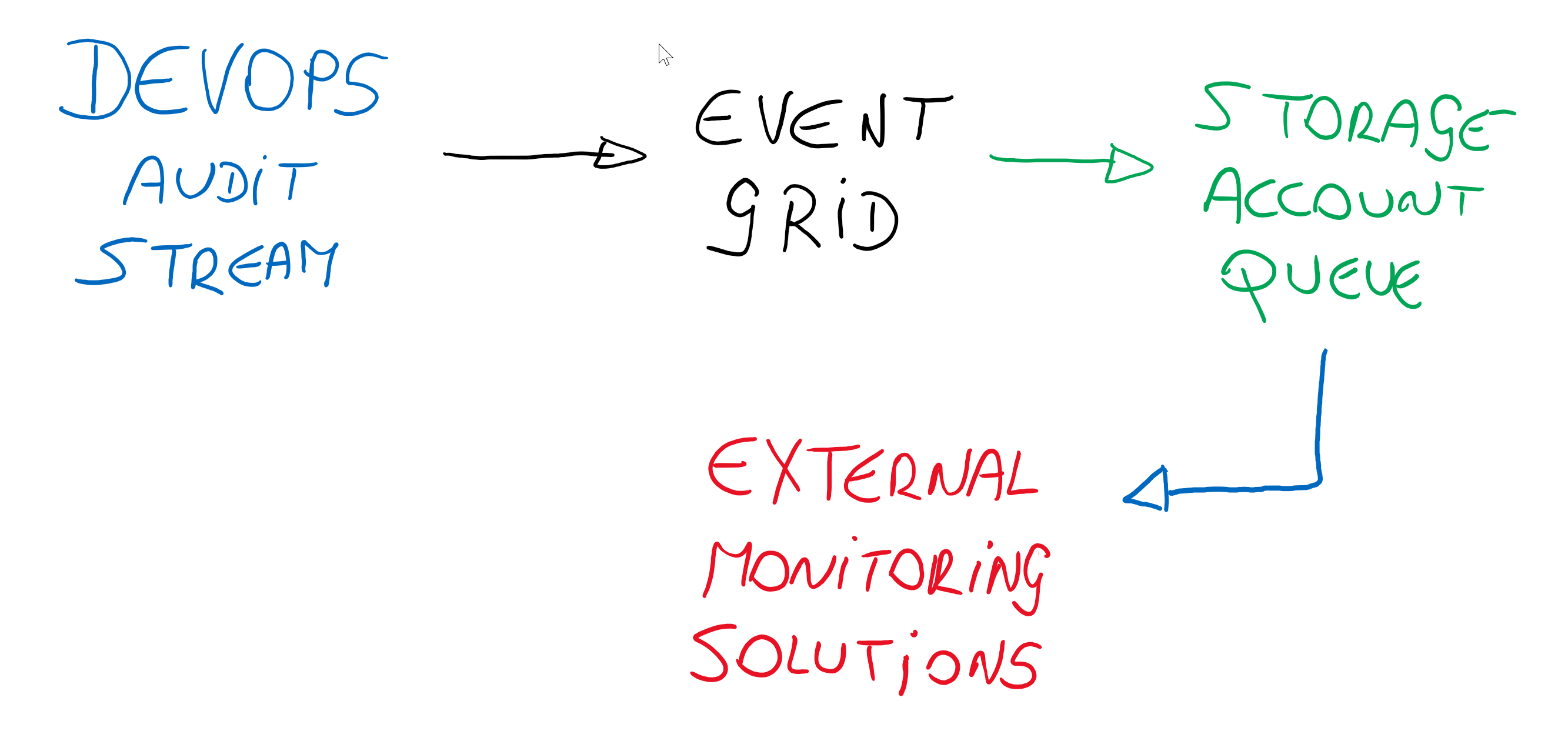
The flow is the following:
- An Auditing event is generated in Azure DevOps
- Auditing Event Stream is configured for Event Grid
- Event Grid transferts the message to an Azure Storage Account Queue (Event Grid can do a lot more though… like triggering Functions, WebHooks)
- From Azure Storage Account Queue, the message could be send along to “any 3rd party monitoring tool”
Walkthrough Setup
Now you do have an idea what Auditing Stream is about, let me guide you through the main steps to see it in action.
Enable Streams
- To enable Streams, open the Organization Settings and navigate to the Auditing menu option. Besides Logs, you should also see Streams
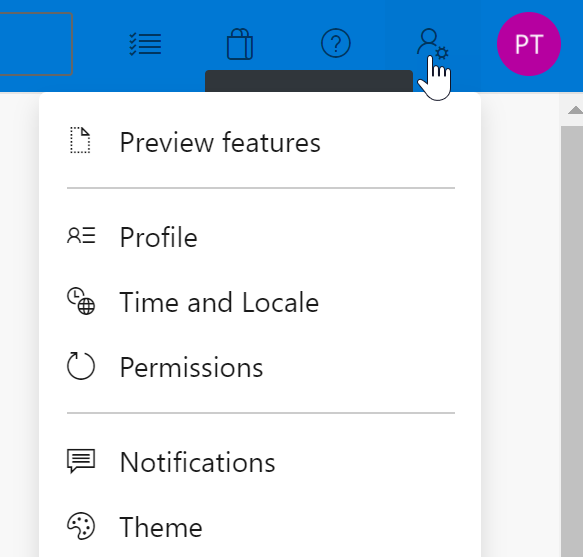
(If you don’t see Streams, make sure you have Azure DevOps Preview Features enabled, which can be validated as follows: From the Azure DevOps Portal, navigate to User Settings (upper right corner next to your user account bubble) and select Preview Features)
- From the Streams window, click the New Stream button, and notice the 3 different options of streaming integration available for now
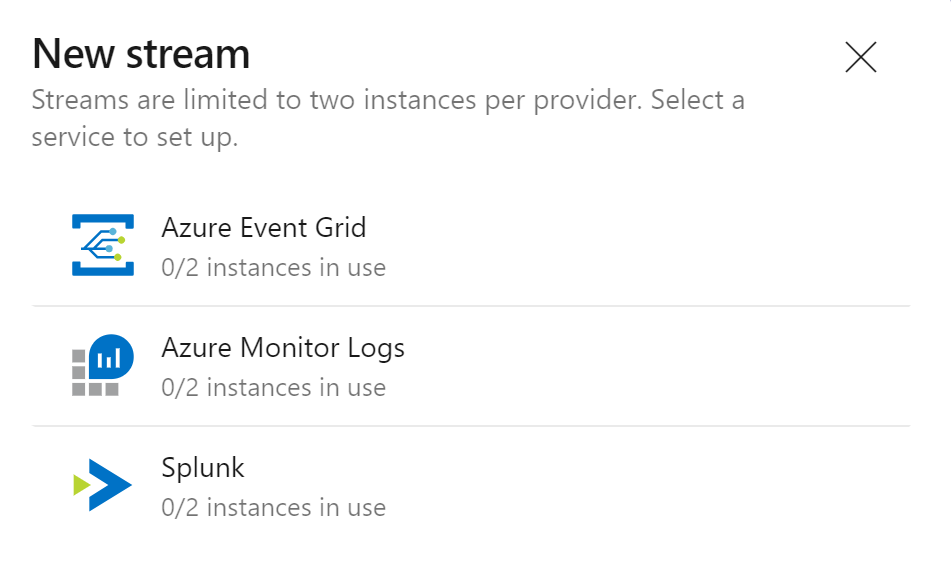
-
Select Azure Event Grid
-
You are asked for the Azure Event Grid Topic URL and Access Key.
Deploy Azure Event Grid Topic
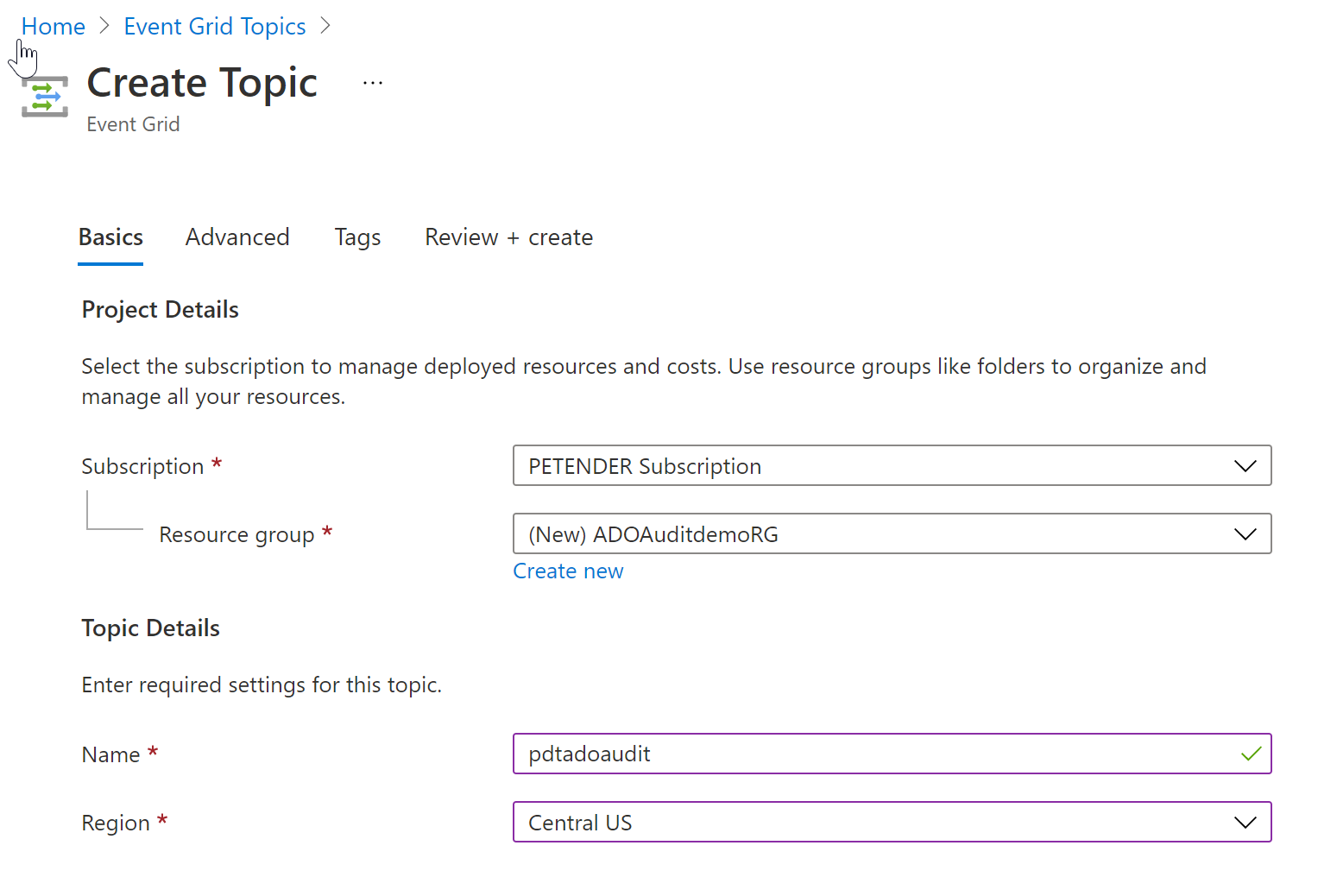
Assuming you don’t have an Azure Event Grid Topic yet, use the following steps to create this resource:
- From the Azure Portal (https://portal.azure.com), search for Event Grid Topic in the “Search Resources, services and docs” field and click the + Create button to deploy a new Event Grid Topic.
- provide the necessary details around Subscription, Resource Group, unique Resource Name and Region for this resource to get created.
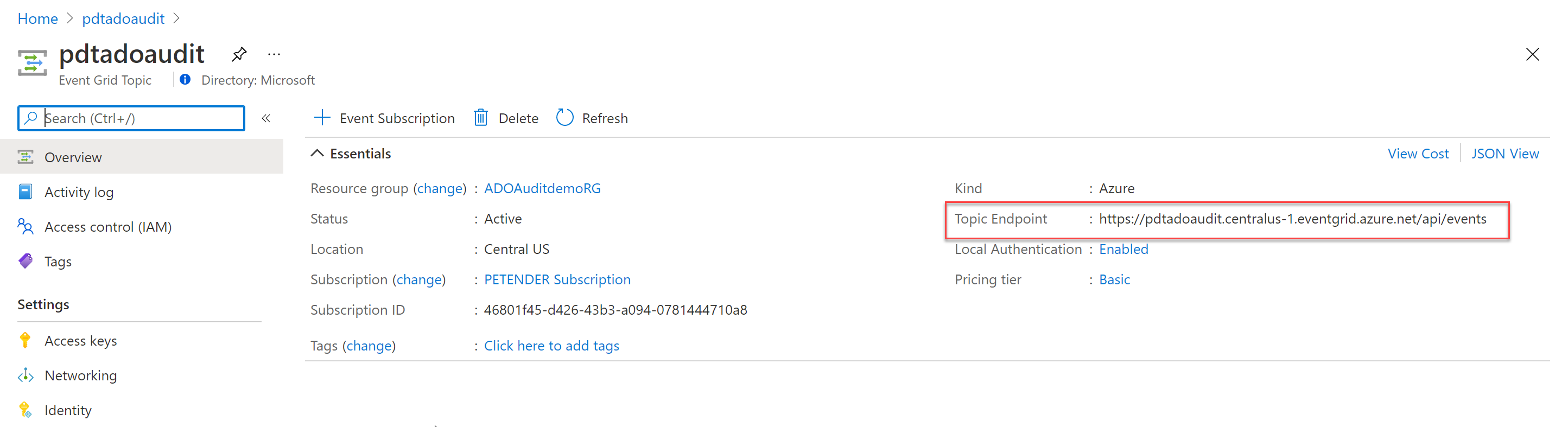
- Wait for the resource to get deployed successfully, and open it in the Azure Portal. Notice the Topic EndPoint under the Overview Blade of Event Grid Topic. This is the URL you need to provide in the Azure DevOps Stream settings for the Event Grid Topic.
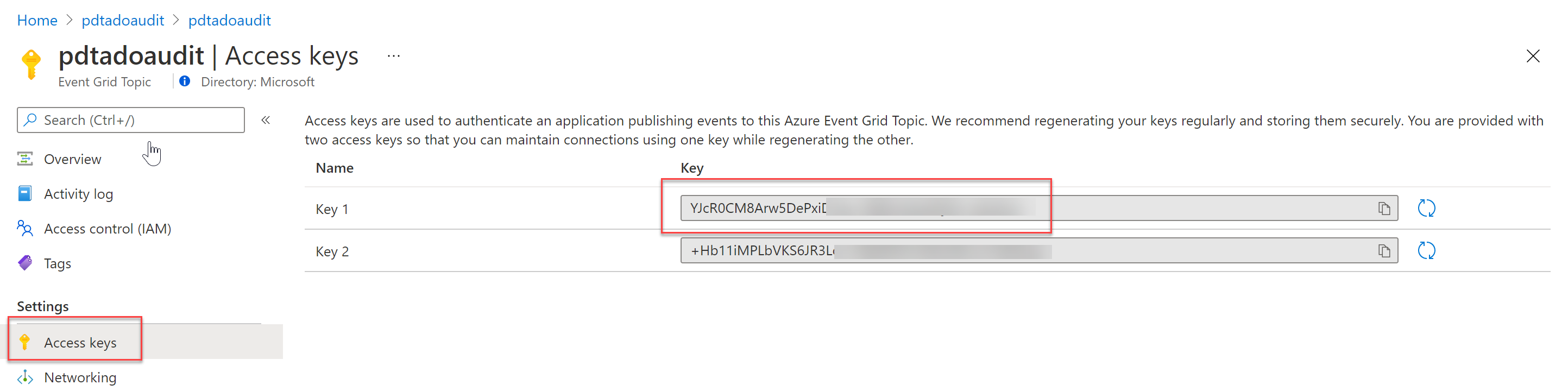
- Navigate to the Access Keys option and copy the Key 1 content to the corresponding field in the Azure DevOps Stream settings for Event Grid Topic.
- The Event Grid settings for Azure DevOps Stream look similar to my sample setup:
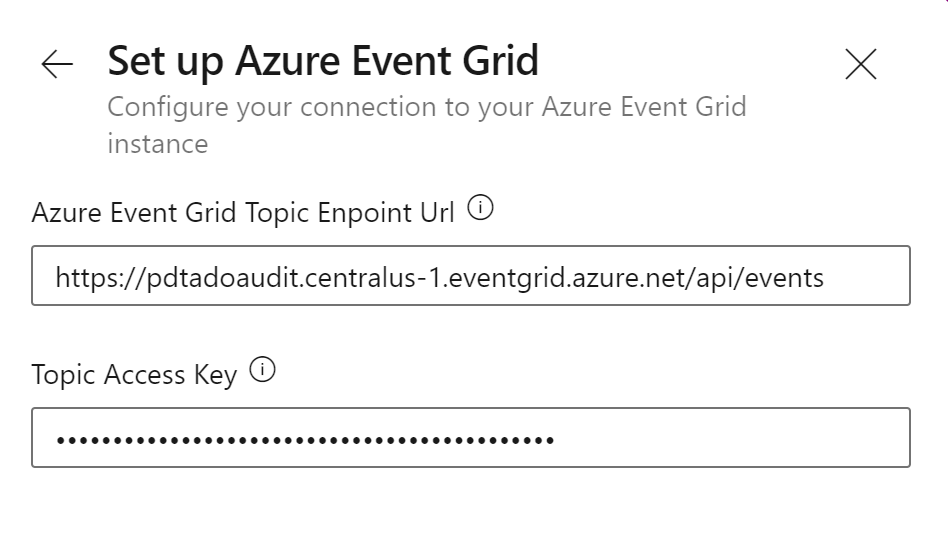
- Save the settings, which creates the Stream integration.
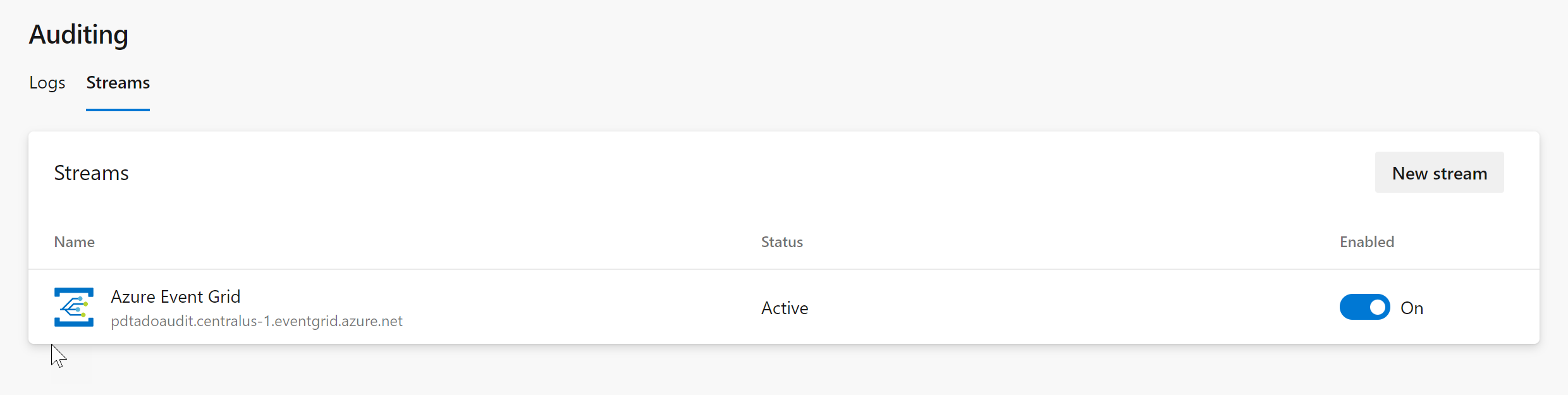
If you would now trigger an Azure DevOps Event, it will get streamed to Azure Event Grid. However, Event Grid has no subscriptions yet, so it has no idea what to do with this receiving information.
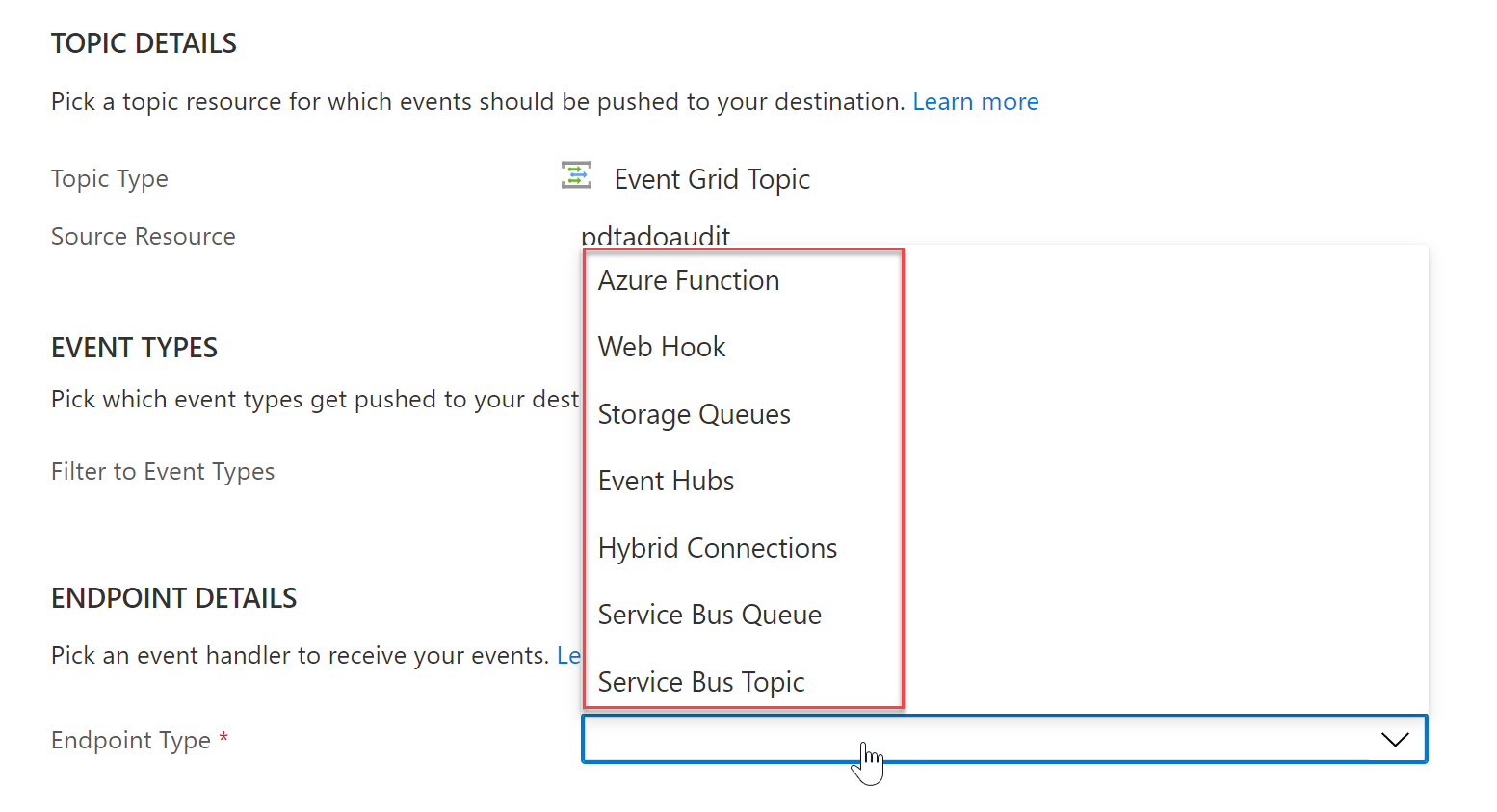
Event Grid supports different EndPoints such as Azure Functions, WebHooks, Service Bus, Storage Queue as targets.
Create Storage Account Queue with Managed Identity
In this example, I will use a Storage Account Queue, but if you have experience with any of the other options, feel free to give that a try.
In order to define this as an EndPoint, let’s create the Storage Account Queue.
-
Create a new Azure Storage Account v2, in the same Location and Resource Group as where the Event Grid Resource got created earlier.
-
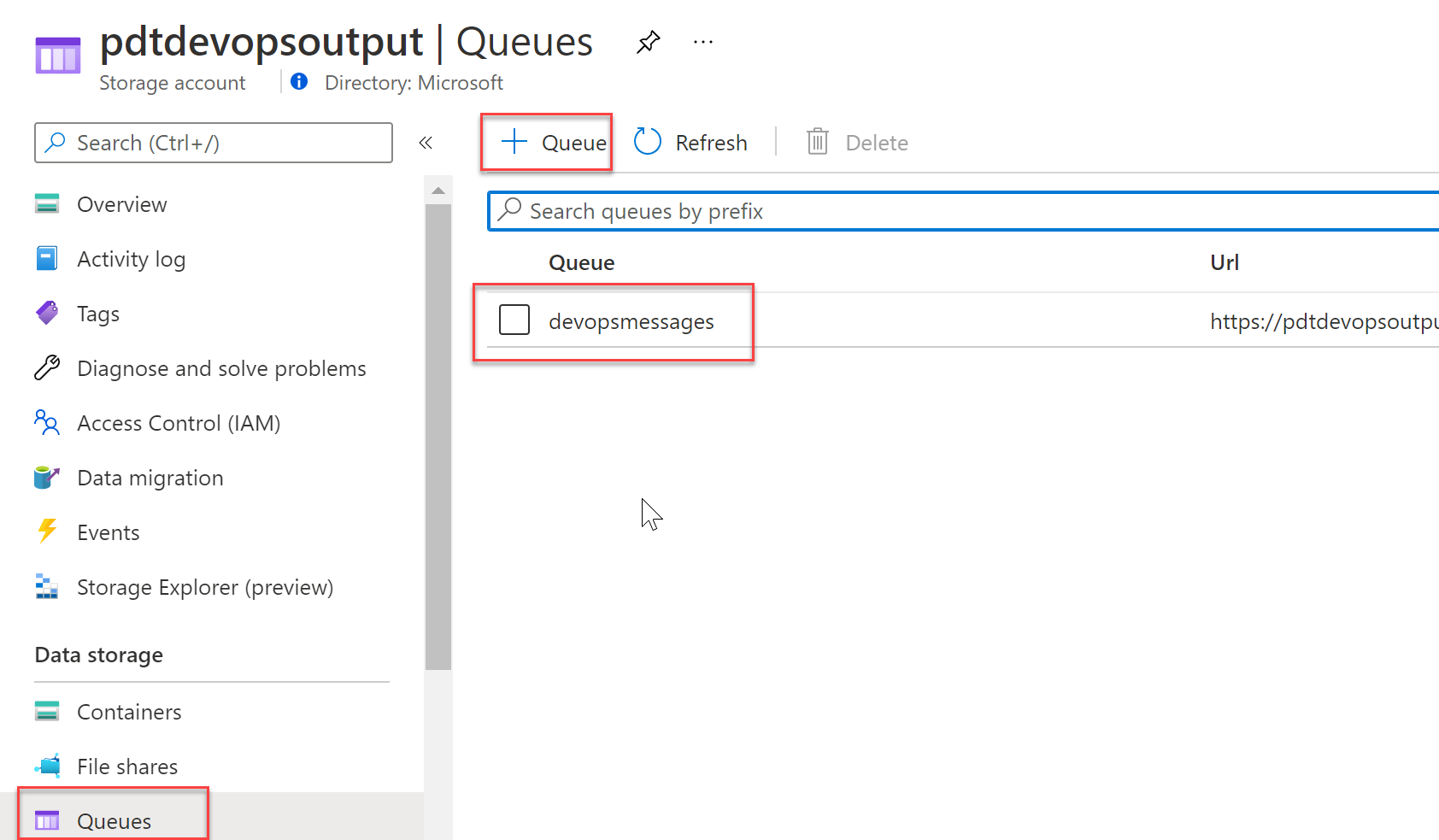
Once the Storage Account is created, navigate to Data Storage / Queue in the Storage Account blade, and create a new Queue. I called mine devopsmessages but it can have any name you want.
To allow the Event Grid Resource to communicate with the Azure Storage Account Queue, I’m using Azure Managed Identity. This relies on the Azure Identity Service Principal concept to authorize both services to communicate with each other.
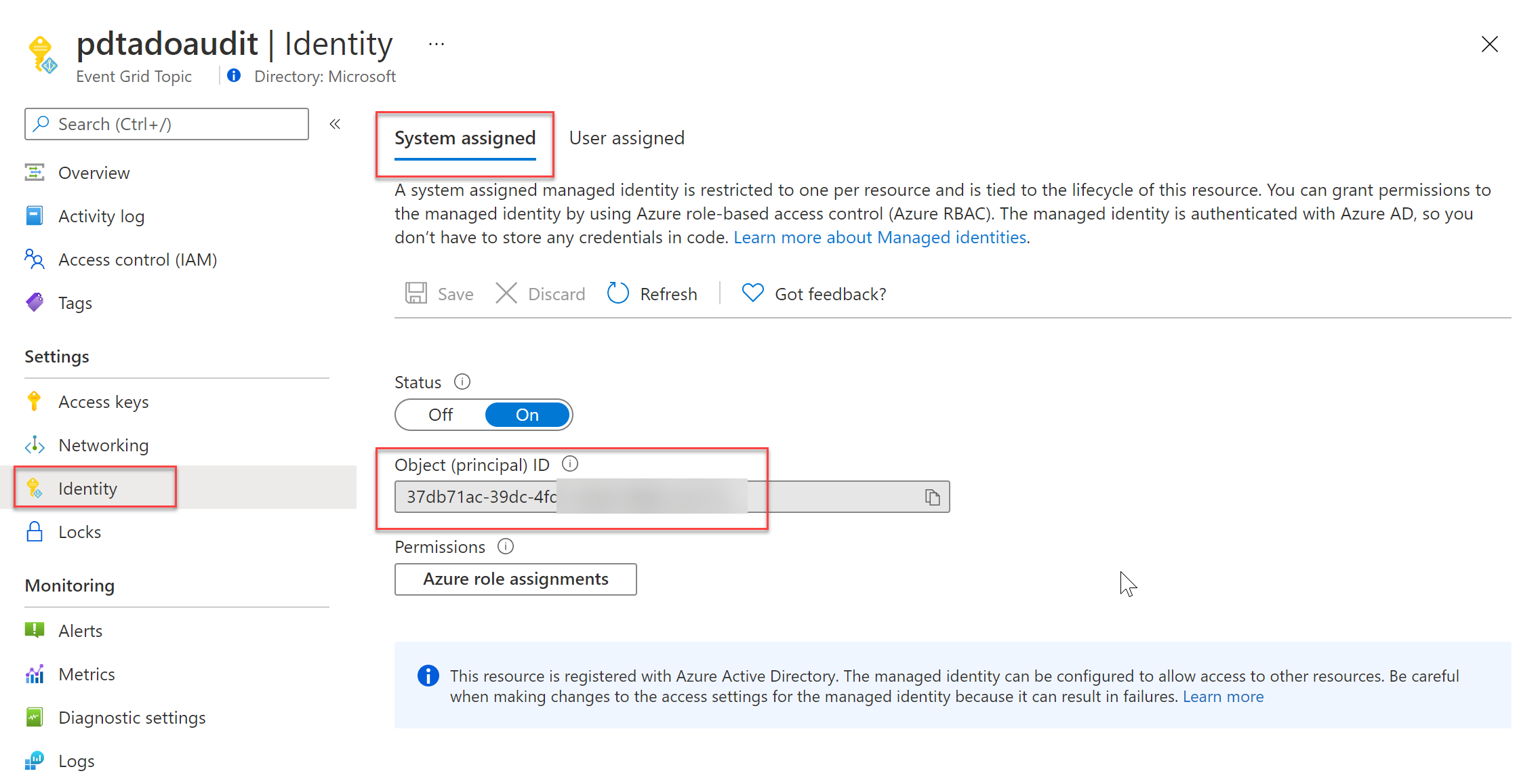
- Navigate back to the Event Grid Topic created earlier, and select Identity under the settings. Next, select System Assigned, which creates a 1-to-1 mapping between the Event Grid Resource and its Azure Identity Service Principal object. Save the changes.
- Navigate back to the Azure Storage Account you created earlier, and select Access COntrol (IAM) from the settings. Specify the following Role Permissions:
- Role: Storage Queue Data Contributor
- Assign access to: User, Group, Service Principal
- Select:
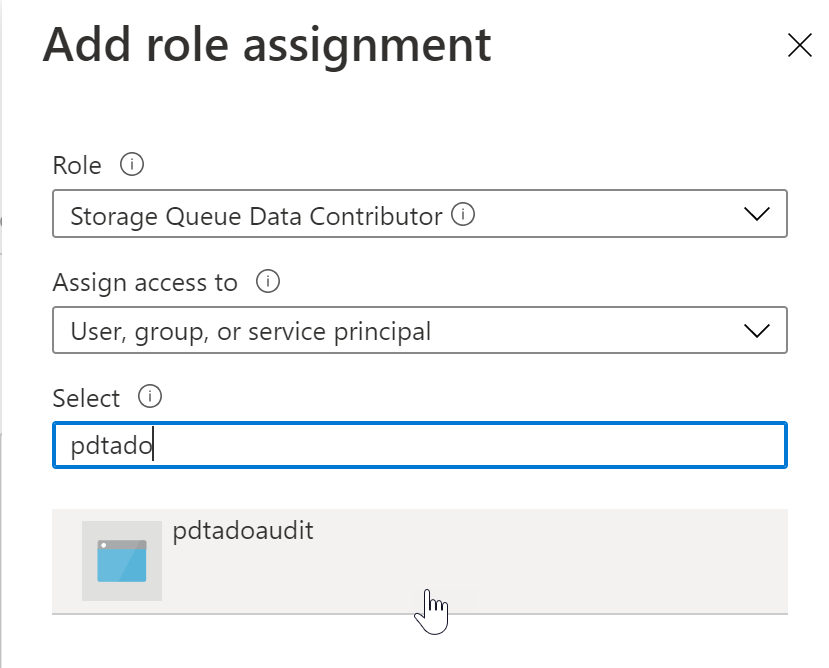
This provides the necessary Role Based Access Control, to allow Event Grid to communicate with the Storage Account Queue, and creating messages in the queue itself.
Configure Event Grid Subscription
In this last step, let’s configure an Event Grid Subscription, which will “listen” for events on the Azure Audit side.
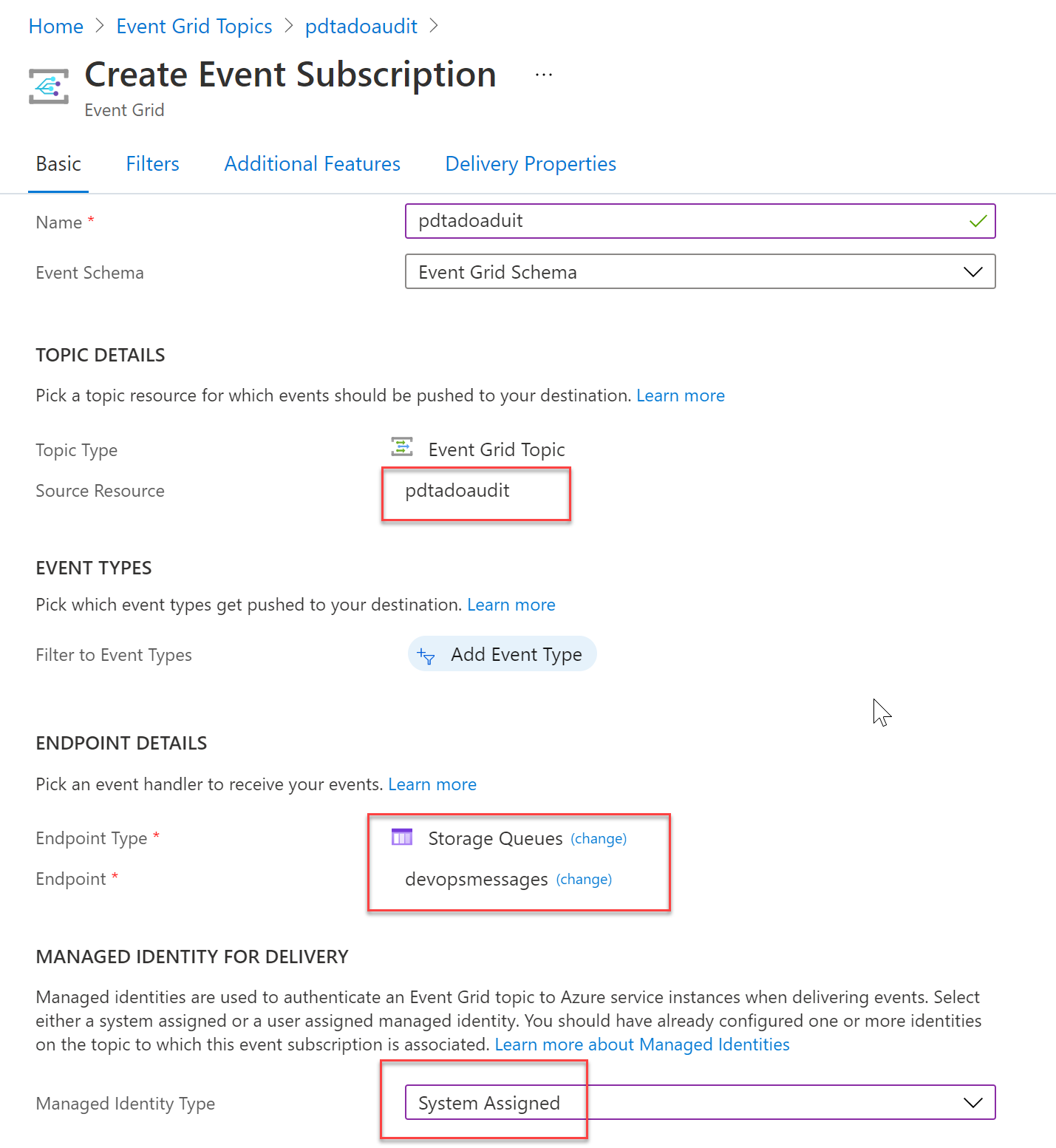
- Open your Event Grid Topic blade, select Overview and click + Event Subscription. Complete the necessary fields with the correct parameters:
- Name: a unique name for the Event Grid Subscription
- Event Schema: Event Grid Schema
- EndPoint Type: Storage Queues
- EndPoint: The Storage Account Queue object
- Managed Identity Type: System Assigned
Here is a screenshot of the settings I used for this article setup:
Monitoring Audit Stream info coming in
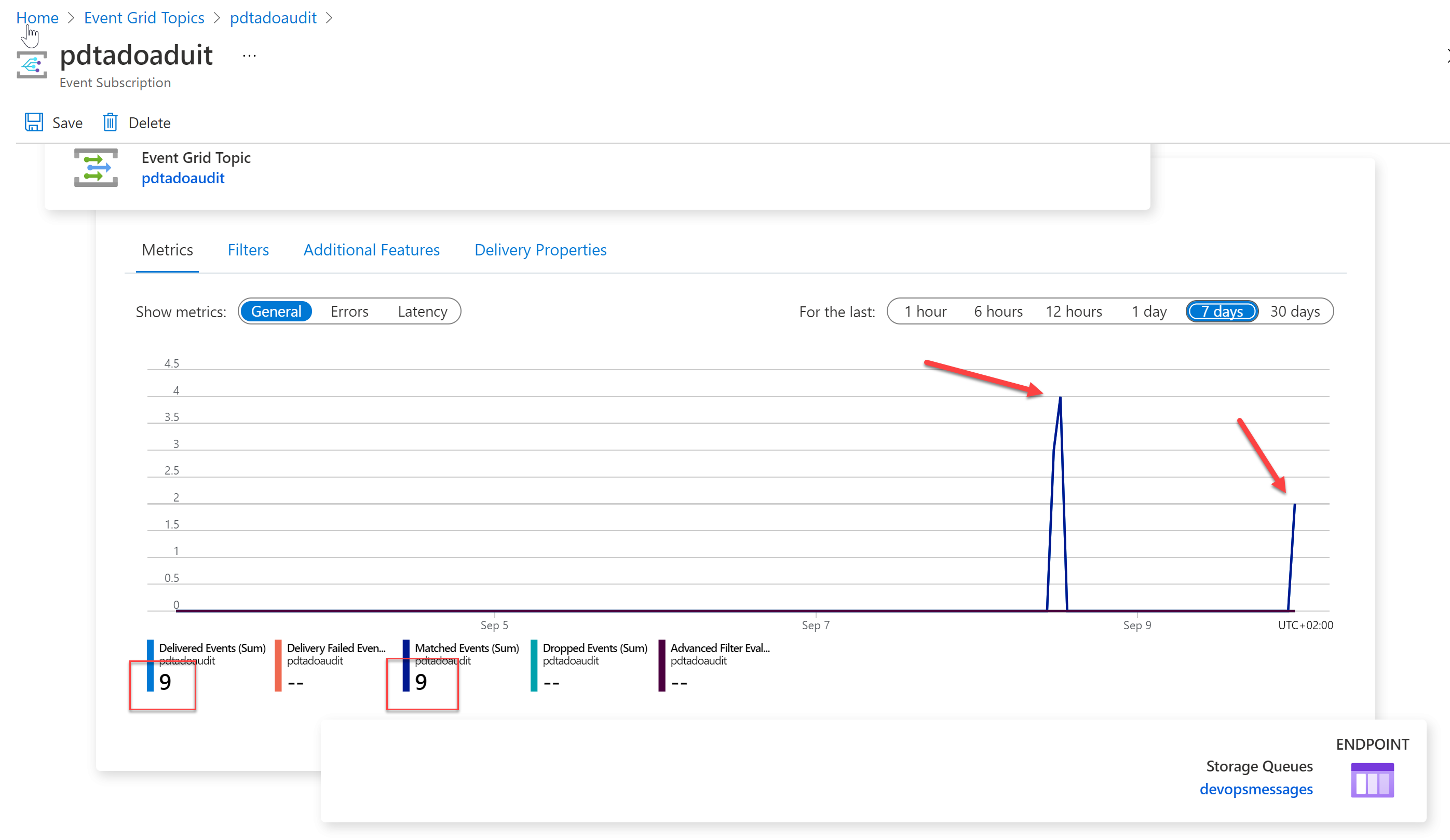
Event Grid and its subcomponent Event Grid Subscription, provide detailed metrics information directly from within the Resource Blade.
-
Generate a few Events on the Azure DevOps side, by for example checking the Audit Log, Trigger a Pipeline run or change Permissions on a Project.
-
After only a few minutes, you should see the events showing up in the Event Grid Topic Overview section:
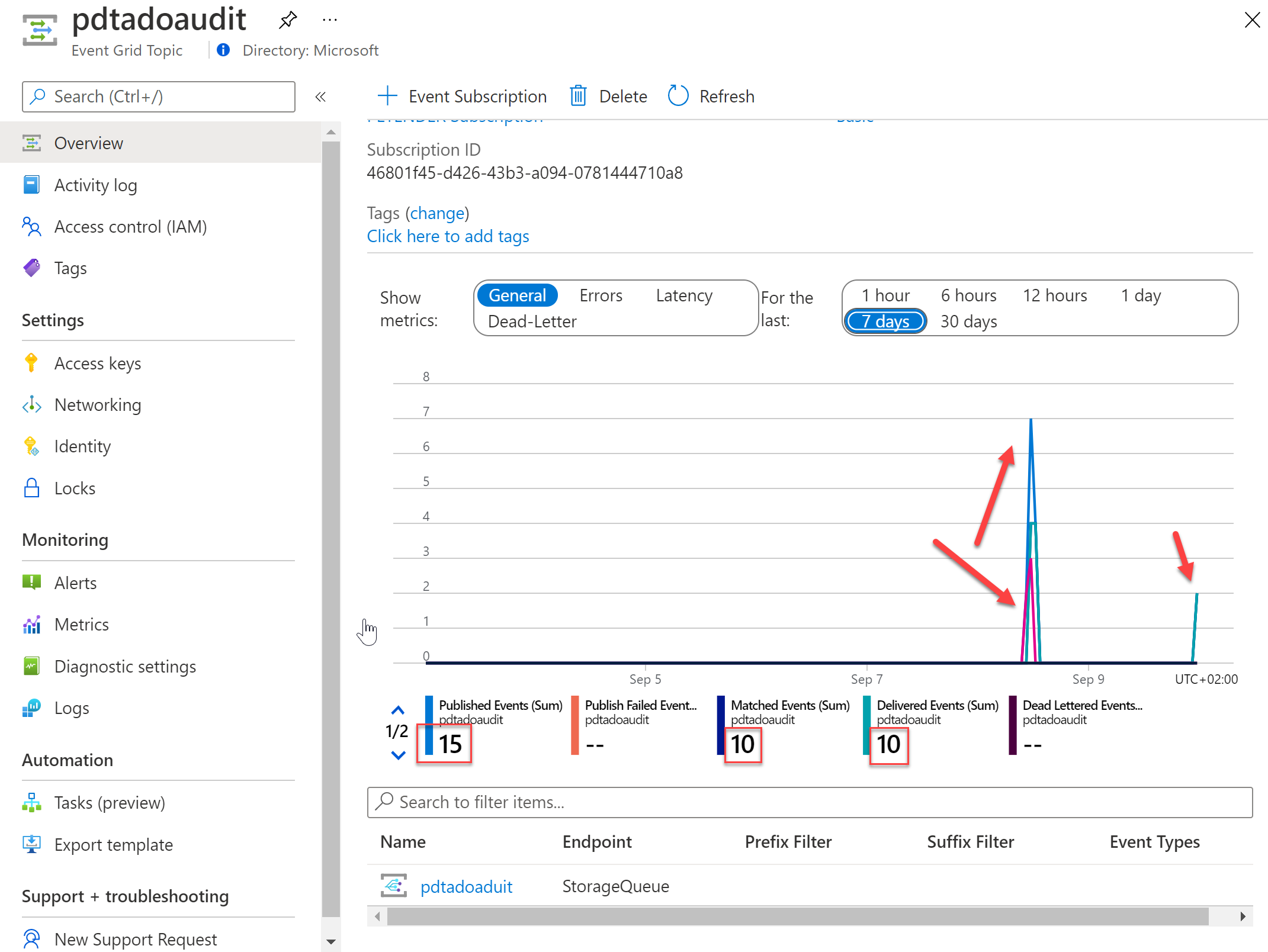
- At the bottom of the chart, select the Storage Queue Subscription object, which redirects you to a more granular dashboard view for the subscription object.
- Last, select the Storage Queues EndPoint underneath the chart, which opens the Storage Account Queue, where you can see the actual DevOps Audit information in a queue message.
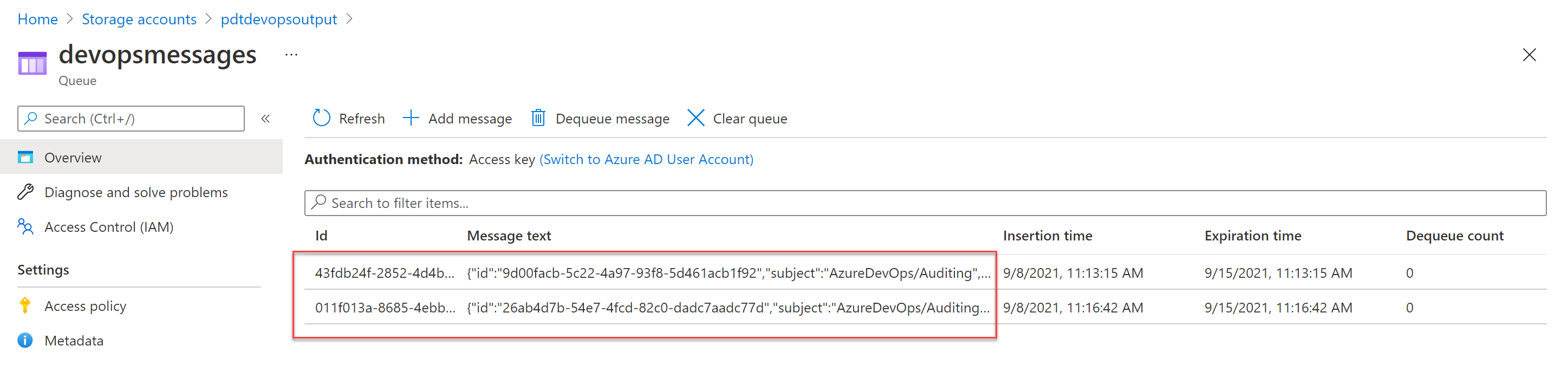
This confirms the setup is complete and Azure DevOps Audit Stream to Event Grid and Storage Queue EndPoint is working as expected.
Summary
In this article, I wanted to introduce you to a new Public Preview feature available in Azure DevOps, namely Audit Stream. This feature allows an organization to stream Auditing information out of Azure DevOps Logs to another solution, for example Azure Event Grid, Azure Monitor Logs or Splunk.
This article covered Event Grid with Storage Account Queue as an example scenario to get you started and get an understanding of the core capabilities. Since Auditing is a crucial component of a healthy platform, I would recommend you to keep your eyes out for any updates on this preview feature, to see it moving to General Availability. If you should have any questions in meantime, do not hesitate to reach out [petender] @ [microsoft.com] or [pdtit] on Twitter.

Very useful! Is there a plan to integrate into an EventHub ? This is what we’re currently using as a central event system in Azure for all Azure logs so our ELK instances can ingest/transform everything.
Hi Alexandre, thanks for the nice feedback. I personally have no idea if a direct stream to event Hub will come in scope, as this is currently still public preview. One option you might look into, is integrating Event Grid with Event Hub – we have a scenario in our Azure Docs: https://docs.microsoft.com/en-us/azure/event-grid/custom-event-to-eventhub. I haven’t tried this myself for the Audit Stream, but since we get the messages in Event Grid, there is basically almost no limit on what happens with them next.
Kind regards, Peter
Useful.