Announcing Azure STIG solution templates to accelerate compliance for DoD
Today we’re announcing the availability of Security Technical Implementation Guide (STIG) solution templates in preview for both Windows and Linux on the Azure Marketplace (commercial) and Azure Government Marketplace. These new templates accelerate speed to achieving Defense Information Systems Agency (DISA) STIG compliance by delivering an automated, one-click solution that enables customers to deploy, monitor, and maintain non-configured STIG-compliant Window or Linux Virtual Machines.
STIG is the Department of Defense’s (DoD) cybersecurity methodology for standardized security configurations for computer operating systems and other software and hardware. DISA releases updated STIGs for various operating systems on a quarterly basis. DoD agencies and contractors are required to use STIG-hardened virtual machines to run software programs and compliance is enforced through the authority-to-operate (ATO) process. Manually implementing this complex methodology often delays cloud consumption.
By providing simple selections, the Azure STIG solution templates fast-track STIG compliance and ultimately aids in cloud adoption.
Benefits of templates include:
- Easy one-click solution simplifies STIG compliance and enables engineering teams to focus on higher priority efforts
- Accelerates speed to DoD STIG compliance
- Hardened according to DISA STIG required configuration standards for security
- Catalyst to cloud transformation
Leverage templates to accomplish following:
- Apply STIG to existing VMs to increase current security footprint
- Deploy to a shared image gallery to support organizational reusability
- Capture detailed logging and analysis of VMs for auditing and authorization purposes.
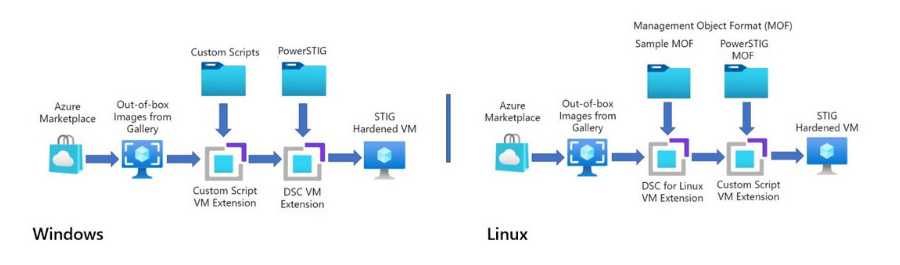
The solution works by leveraging out-of-box (OOB) images from the Azure Marketplace gallery to reduce the complexity involved with maintaining custom images. Desired state configuration is leveraged with PowerSTIG and several VM extensions to produce pre-hardened images. The resulting VMs are 90%+ STIG compliant after a successful deployment. The templates are composed of ARM templates and a custom UI to give users a native Azure portal VM deployment experience. Diagnostic logging can be optionally stored in a storage account and/or a Log Analytics workspace to provide detailed auditing information.
The solution supports the deployment of Windows 10, Windows 10 multi-session, Windows Server 2019, Windows Server 2016, CentOS 7x, RHEL 7x, and Ubuntu 1804, Ubuntu 1804 Data Science.
We plan to integrate the solution with Azure Policy in the future to provide the ability to monitor and maintain the security footprint after deployment, allowing you to ensure limited to no compliance drift on your VMs.
Get started today with Azure STIG solution templates:
| Windows | Linux |
| Azure commercial | Azure commercial |
| Azure Government | Azure Government |
| Azure Government Secret (coming soon!) | Azure Government Secret (coming soon!) |
For any additional questions and to provide feedback, please reach out to AzureSTIGSupport@microsoft.com.

 Light
Light Dark
Dark
0 comments